Azure Key Vault safeguards encryption keys and secrets like certificates, connection strings, and passwords.
Key vaults define security boundaries for stored secrets. It allows you to securely store service or application credentials like passwords and access keys as secrets. All secrets in your key vault are encrypted with a software key. When you use Key Vault, you no longer need to store security information in your applications. Not having to store security information in applications eliminates the need to make this information part of the code.
What is a secret in Key Vault?
In Key Vault, a secret is a name-value pair of strings. Secret names must be 1-127 characters long, contain only alphanumeric characters and dashes, and must be unique within a vault. A secret value can be any UTF-8 string up to 25 KB in size.
Vault authentication and permissions
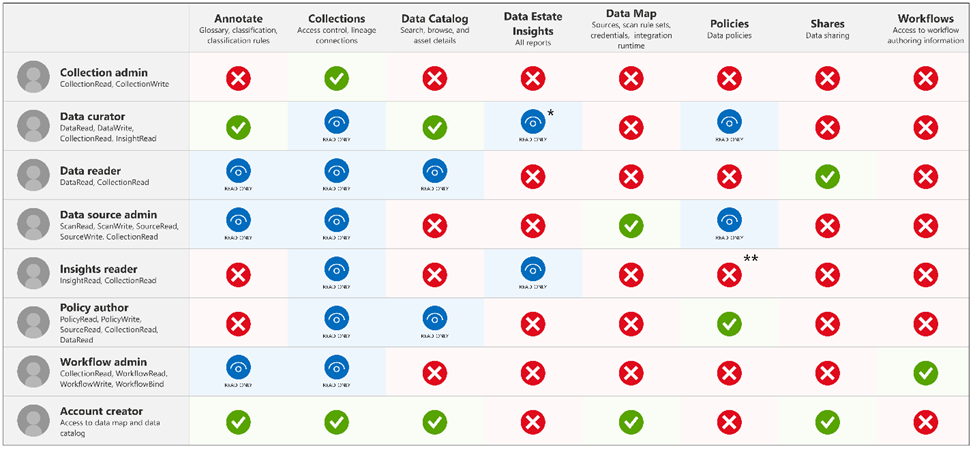
Developers usually only need Get and List permissions to a development-environment vault. Some engineers need full permissions to change and add secrets, when necessary.
For apps, often only Get permissions are required. Some apps might require List depending on the way the app is implemented. The app in this module’s exercise requires the List permission because of the technique it uses to read secrets from the vault.
In this article, we will focus on 2 sections, set up secrets in Key Vault and application retrieves secrets that ware saved in Key vault.
Create a Key Vault and store secrets
Creating a vault requires no initial configuration. You can start adding secrets immediately. After you have a vault, you can add and manage secrets from any Azure administrative interface, including the Azure portal, the Azure CLI, and Azure PowerShell. When you set up your application to use the vault, you need to assign the correct permissions to it
Create a Key Vault service
To create Azure Key Vault service, you can follow the steps.
From Azure Portal, search “key Vault”
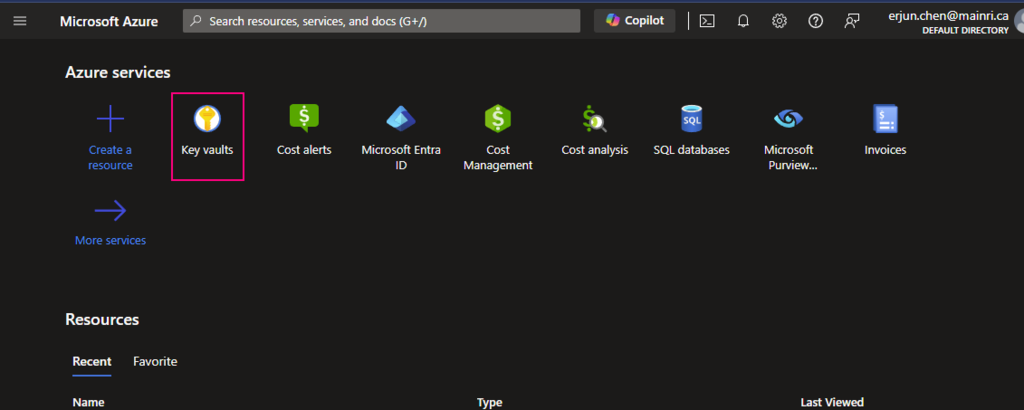
click “key Vault”
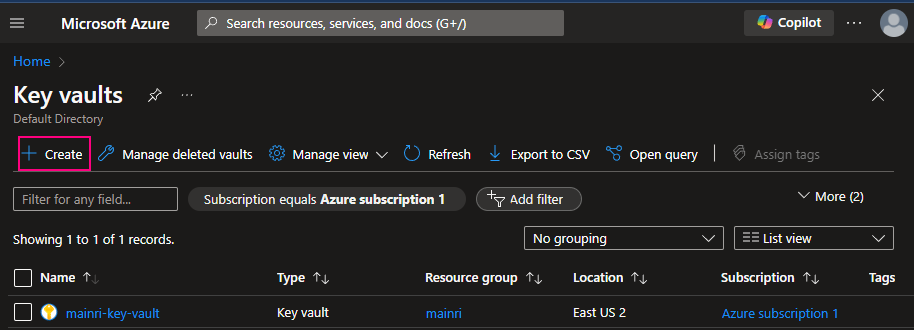
Fill in all properties

Click review + create. That’s all. Quite simple, right?
Create secrets and save in Key Vault
There are two ways to create secret and save in Key vault.
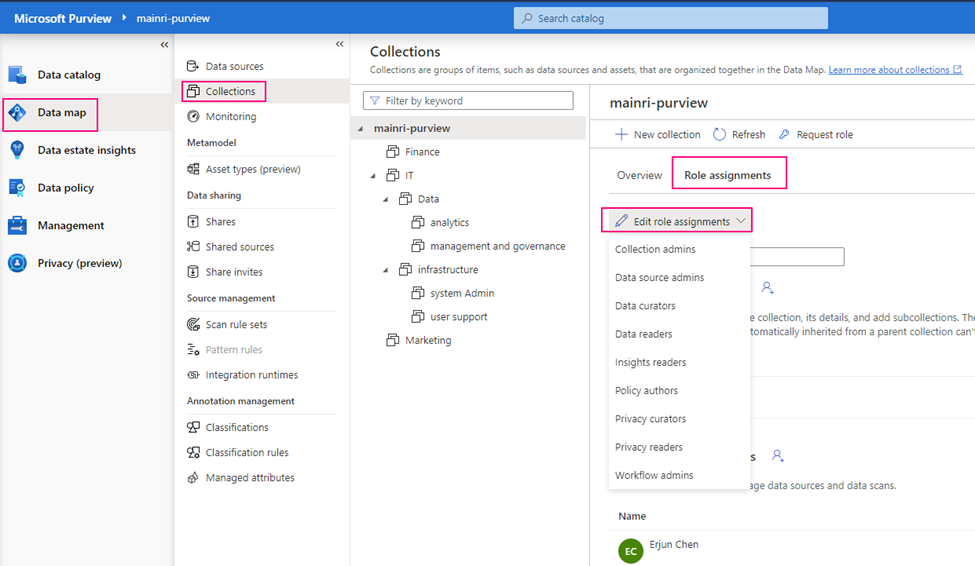
- Access control, Identity and Access management (IAM)
- Access Policies
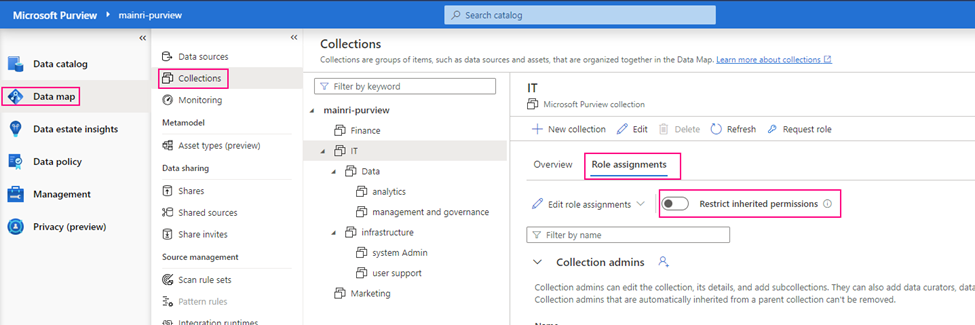
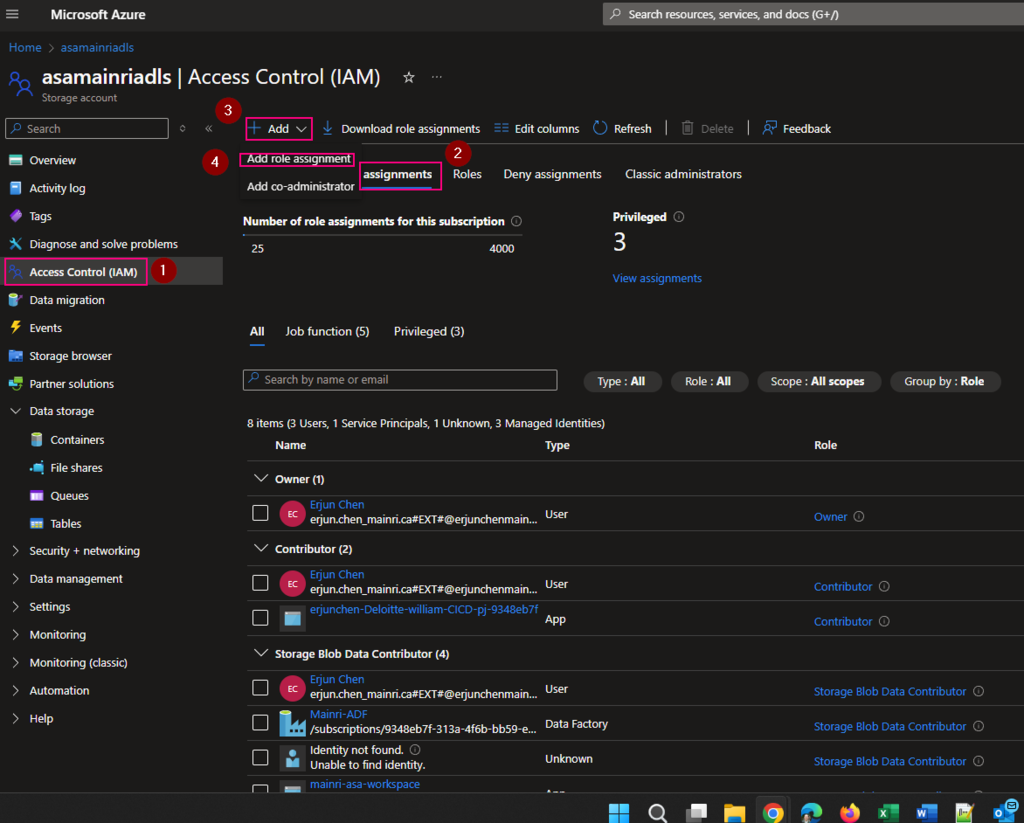
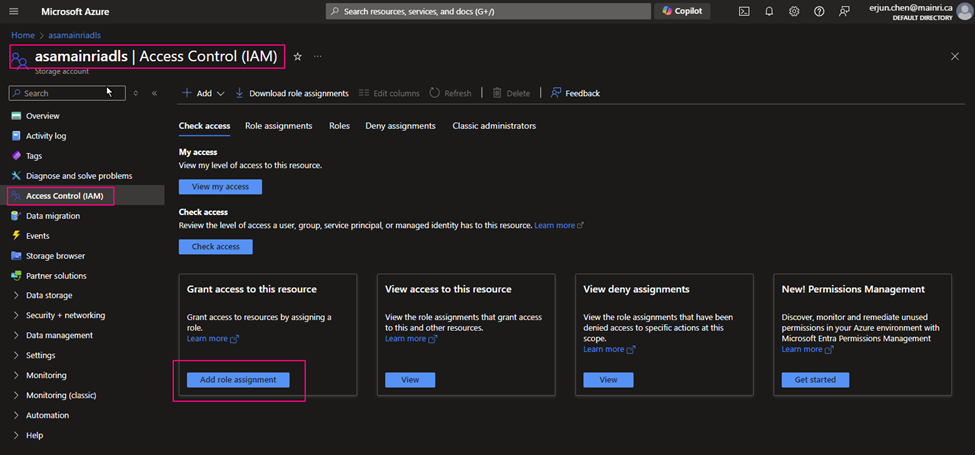
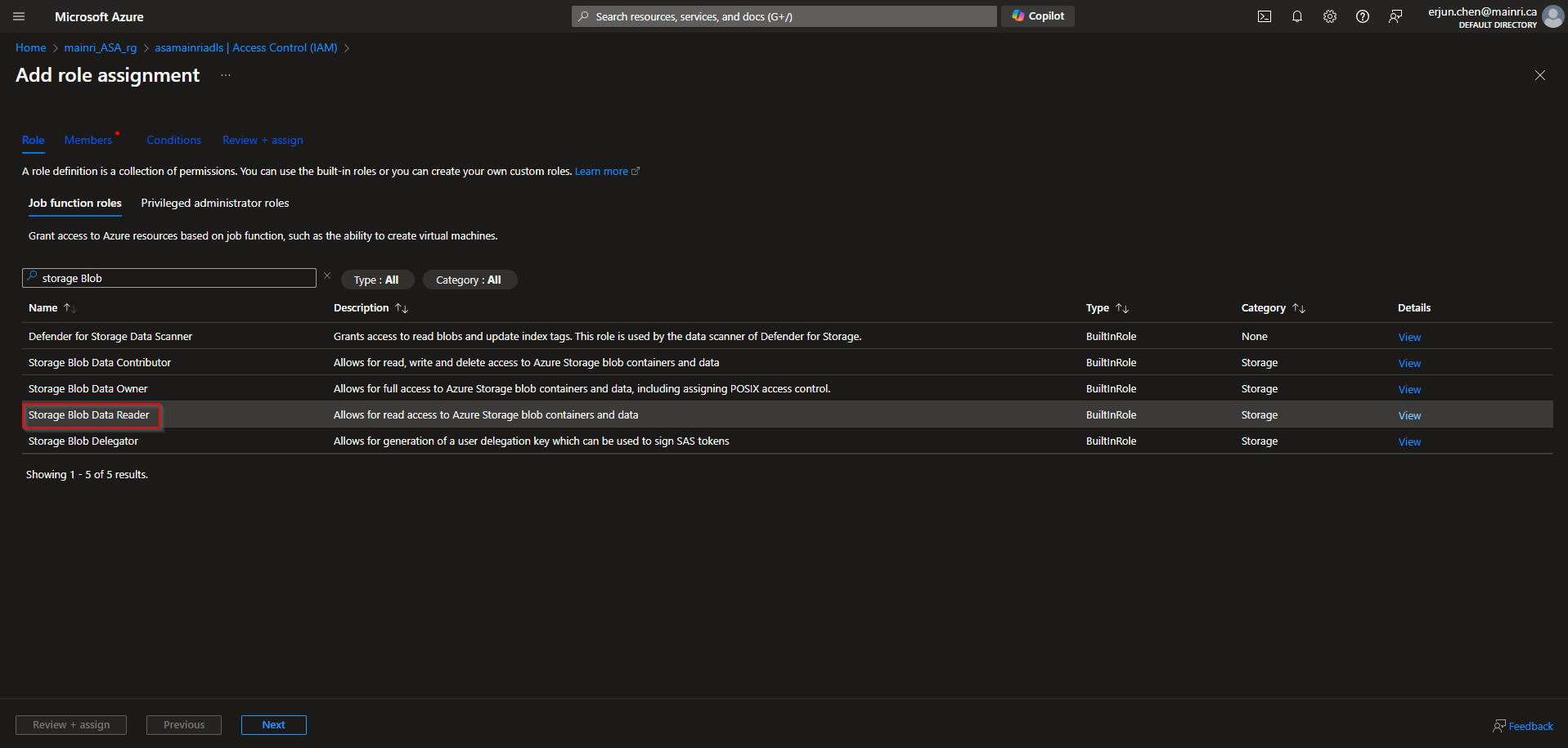
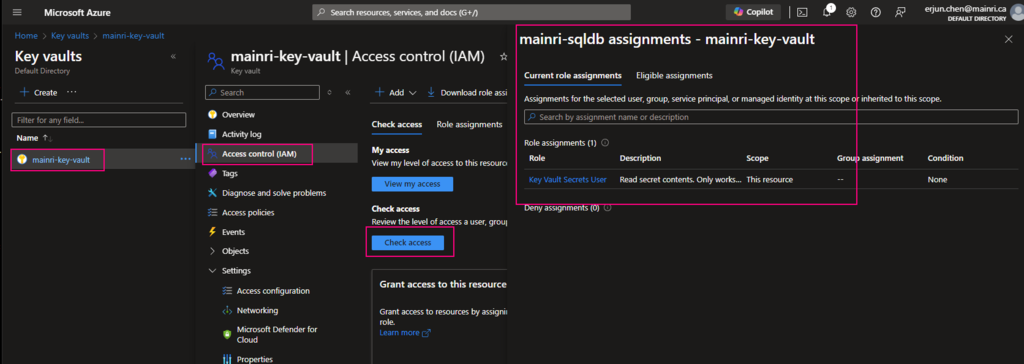
Using Access Control (IAM) create a secret
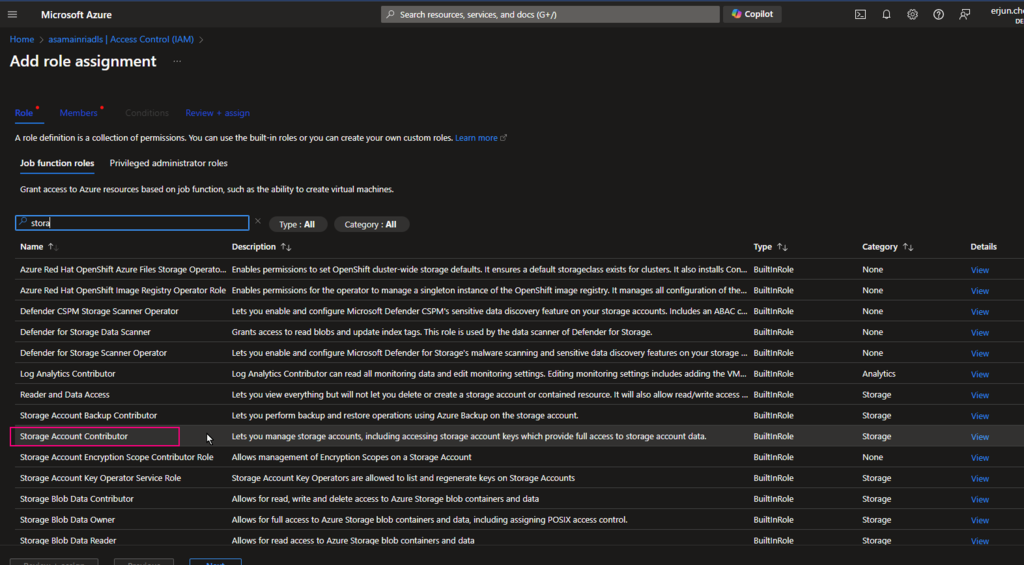
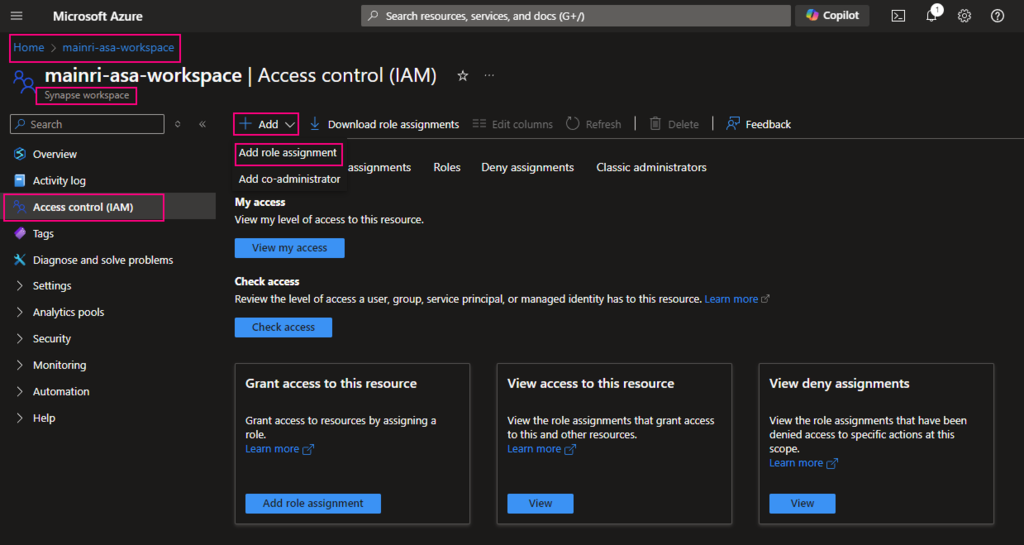
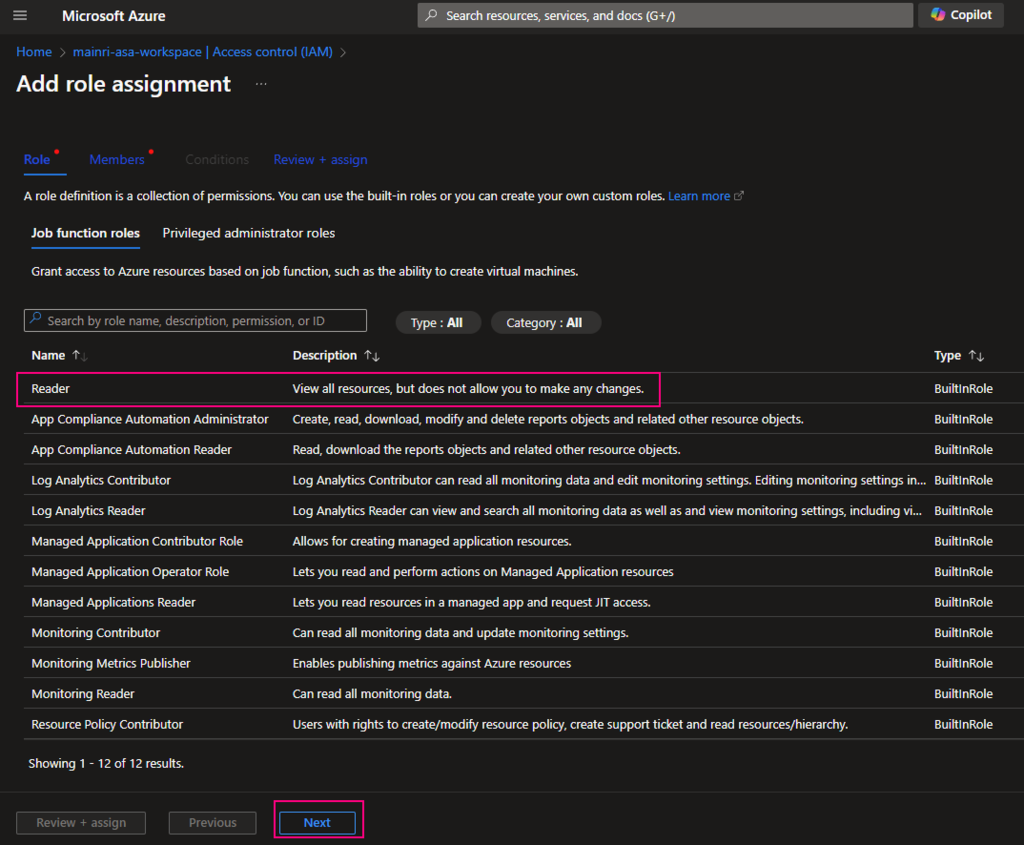
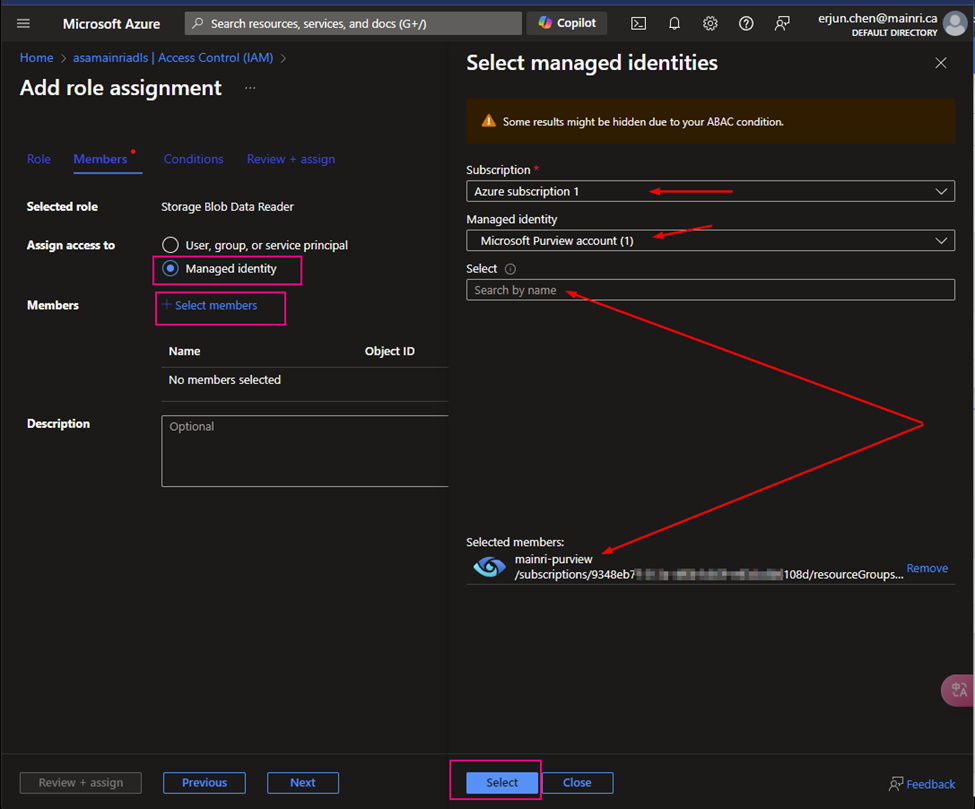
From Key Vault> Access Control (IAM) > Add role Assignment
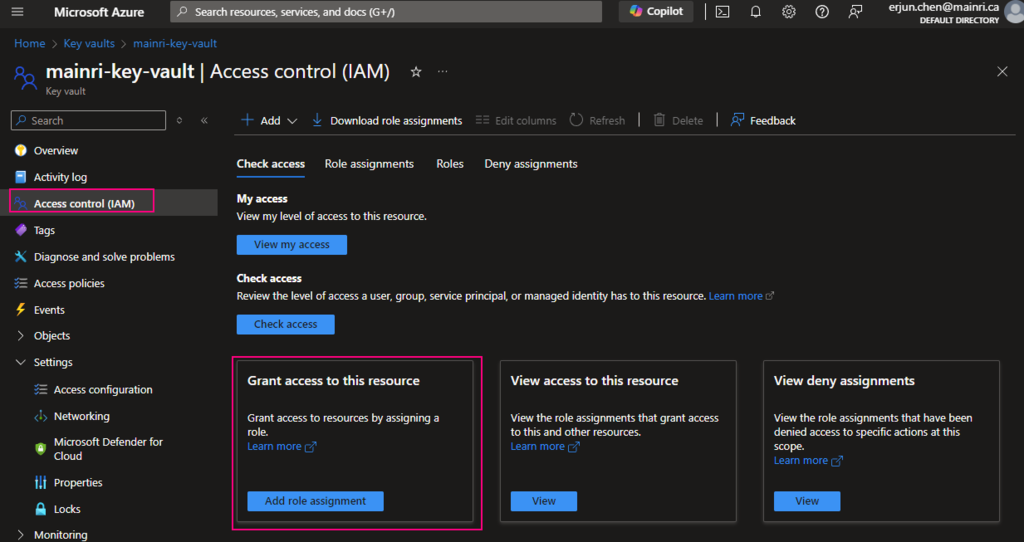
In most cases, if you create and save secrets in key-vault for your users to use, you only need add the “Key vault secrets user” role assignment.
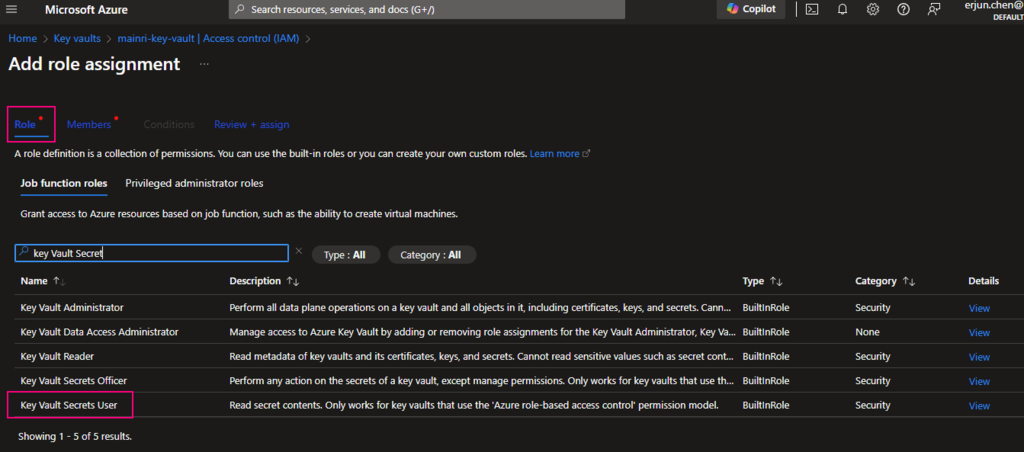
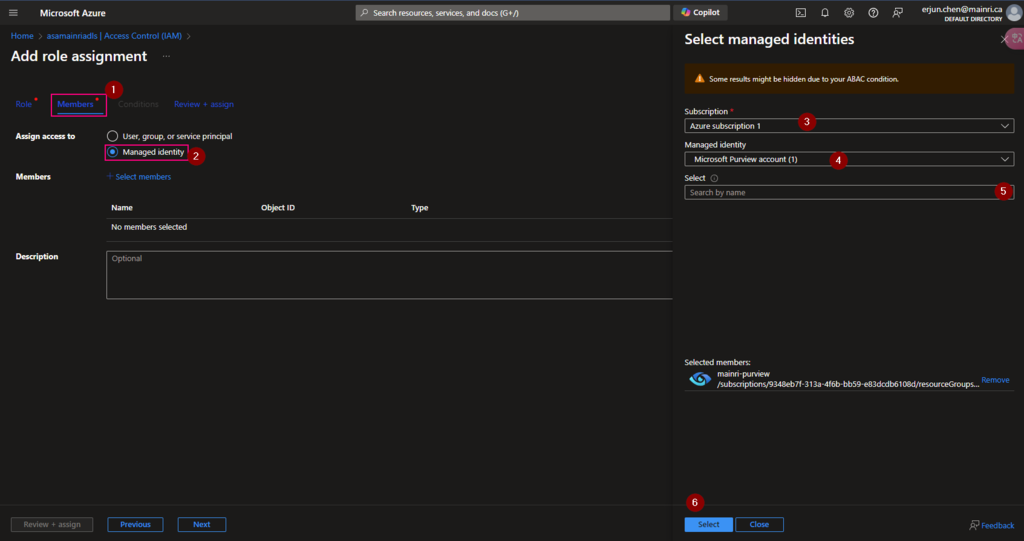
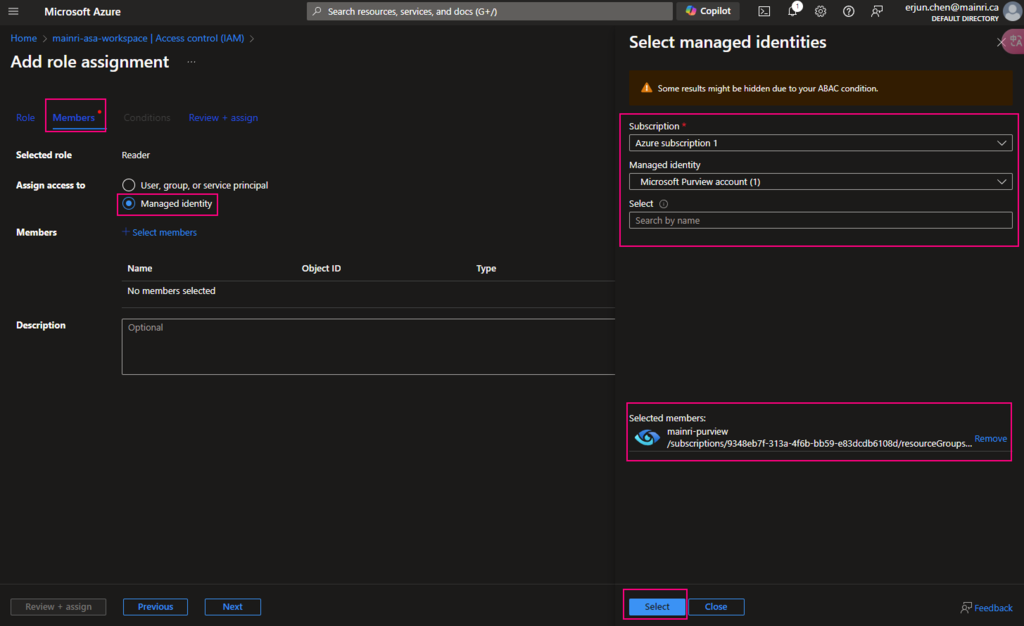
click “next” select a member or group
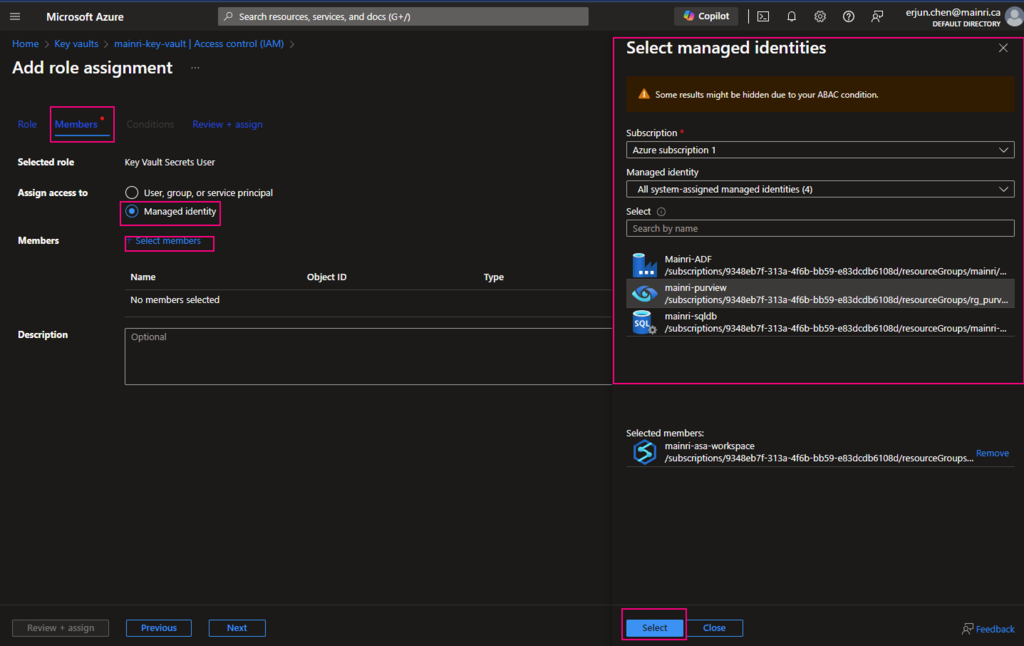
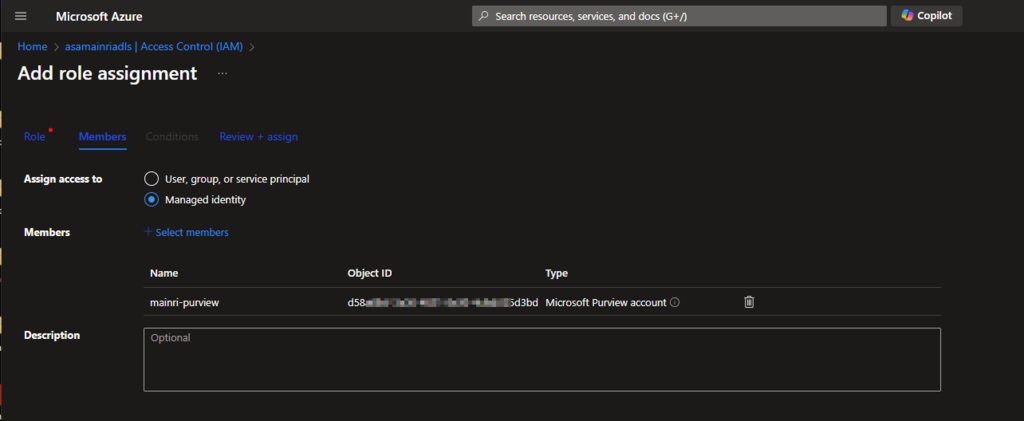
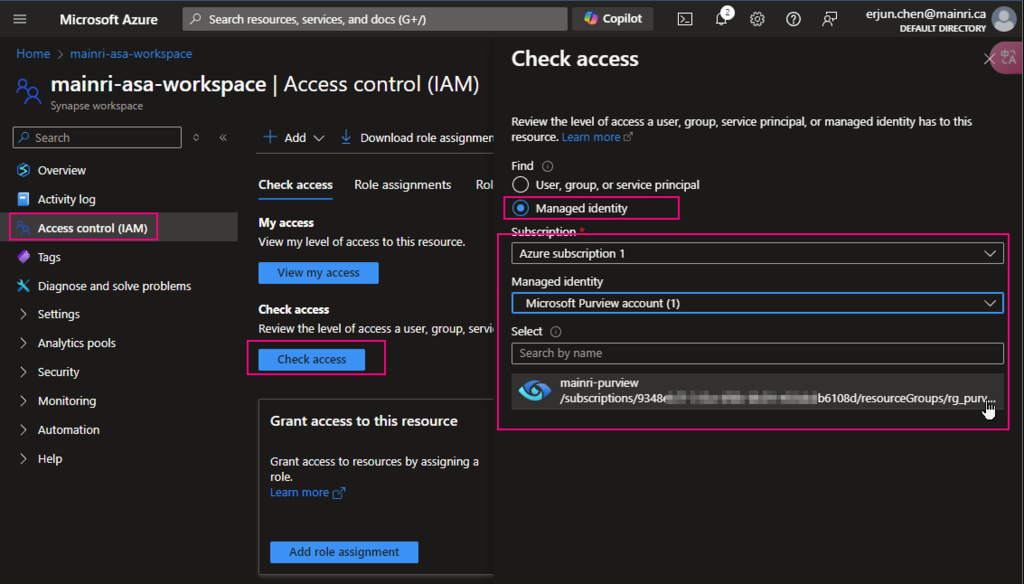
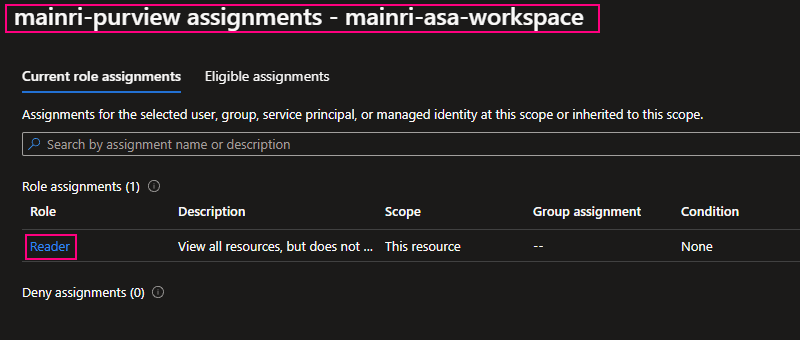
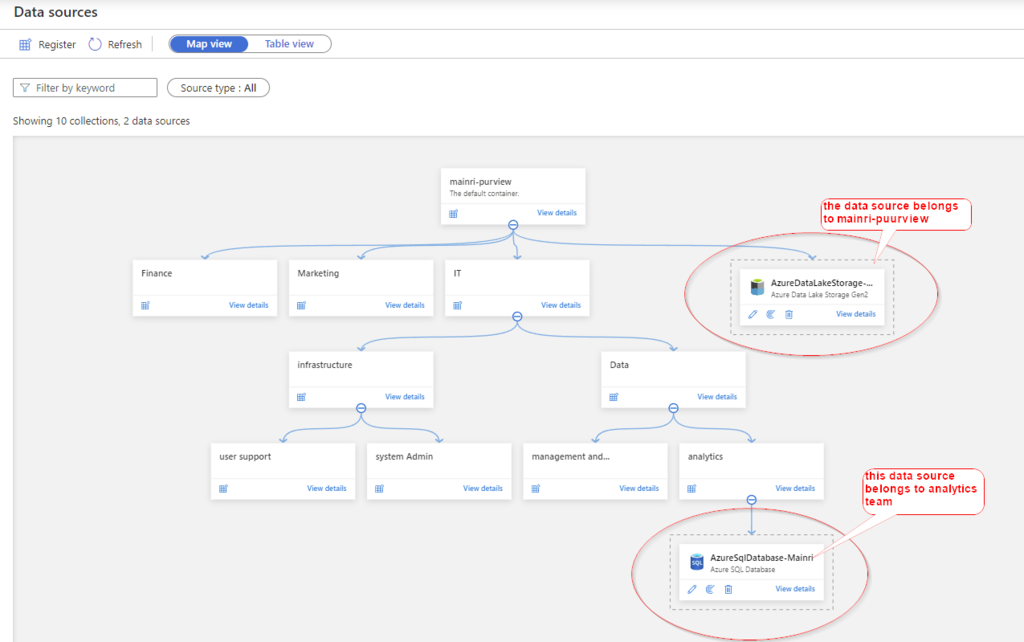
Pay attention to here, if your organization has multiple instances of the same services, for example, different teams are independently using different ADF instants, make sure you correctly, accurately add the right service instant to access policies.
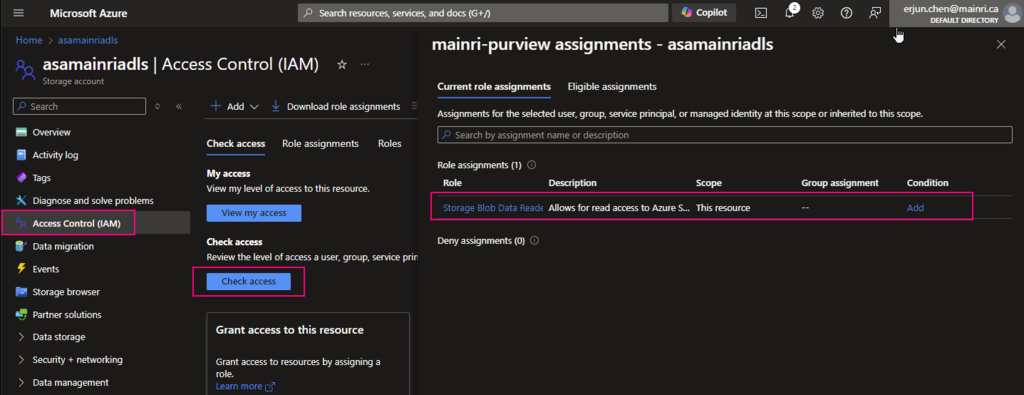
Once it’s down, check the access.
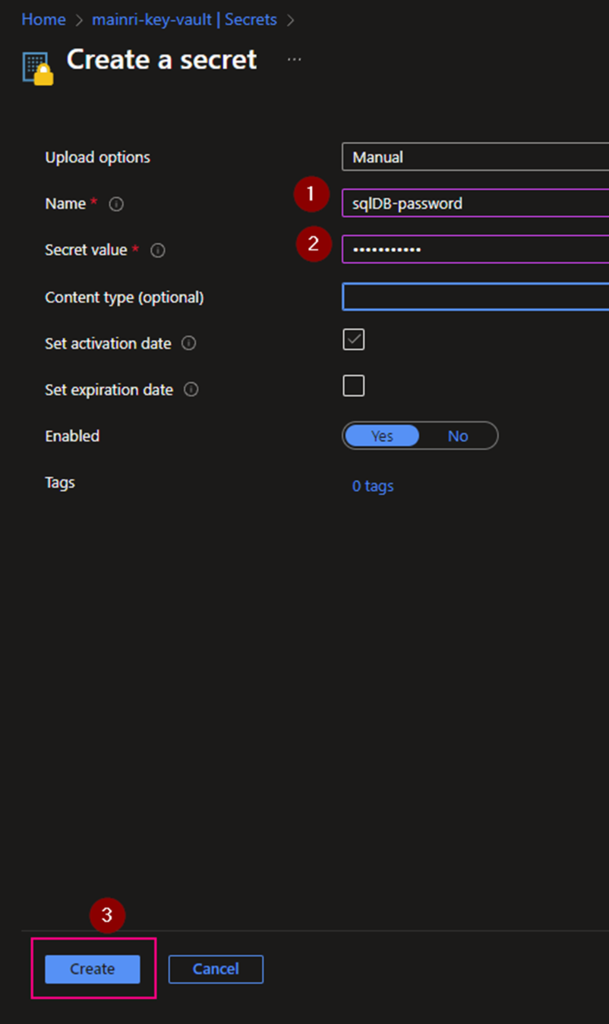
Create a Secret
From “Key Vault” > “Object” > “Secrets” > “+ Generate/Import”
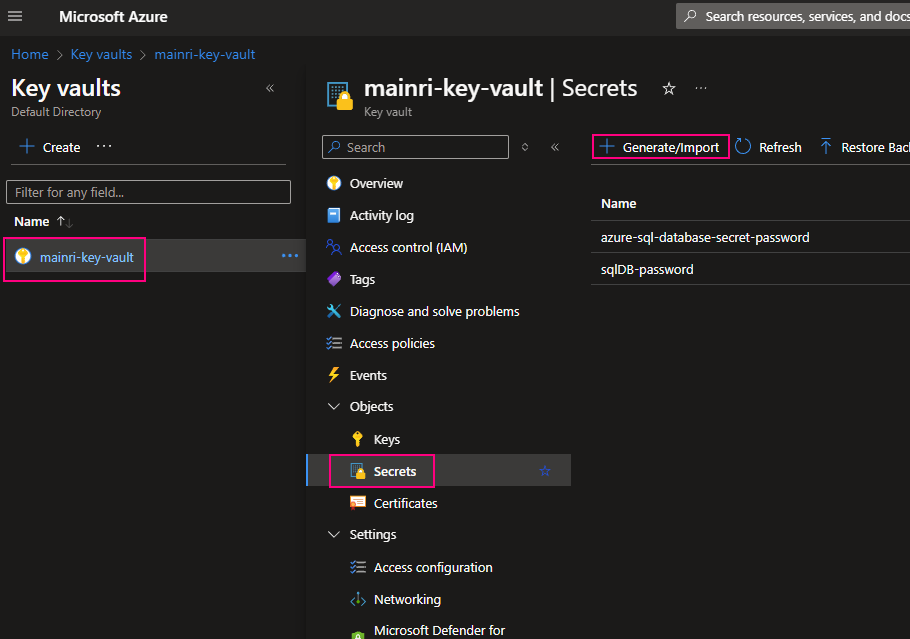
Fill in all properties, :Create”
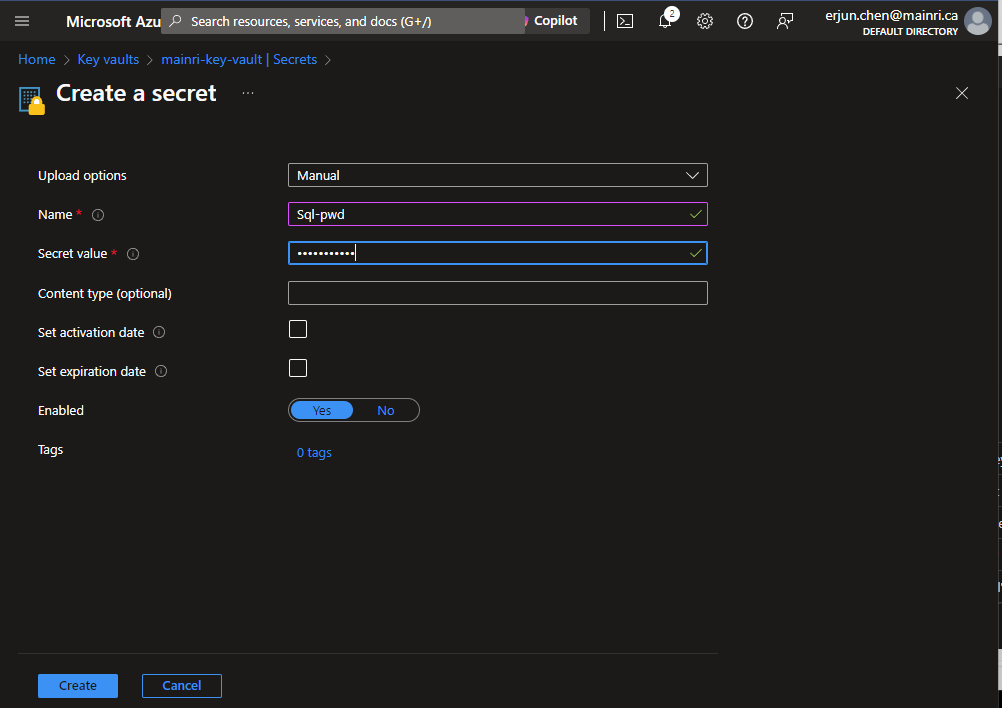
Secrets key and value created That’s all.
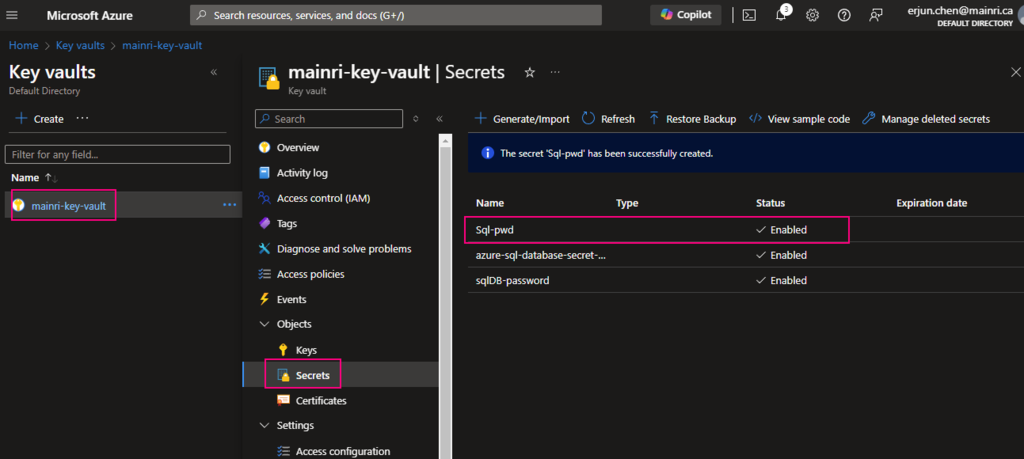
If you want to update the secret, simply click the key, follow the UI guide, you will not miss it.
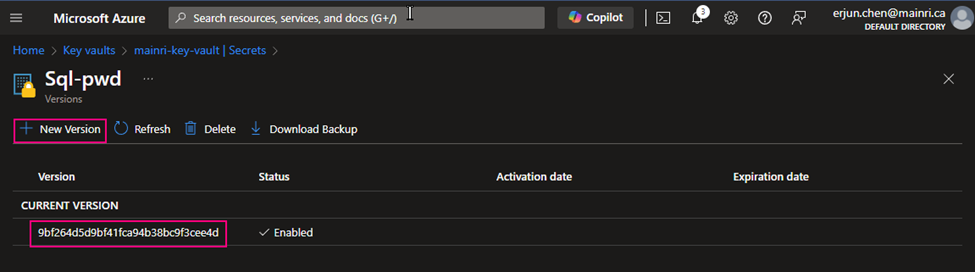
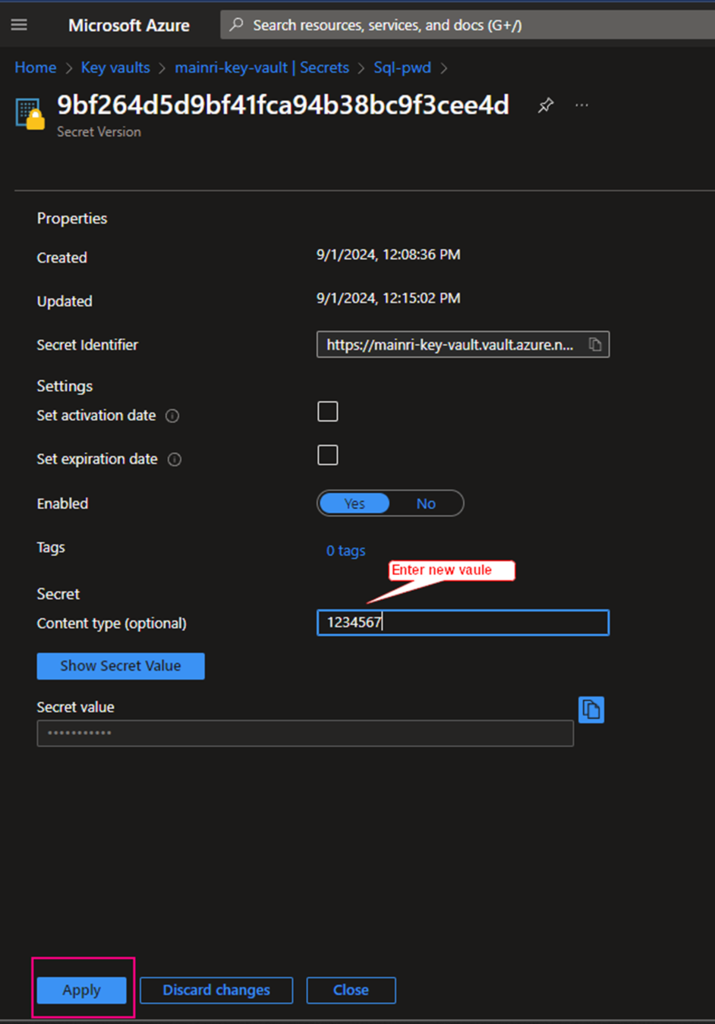
Click the “version” that you want to update. Update the content > apply it.
That’s all.
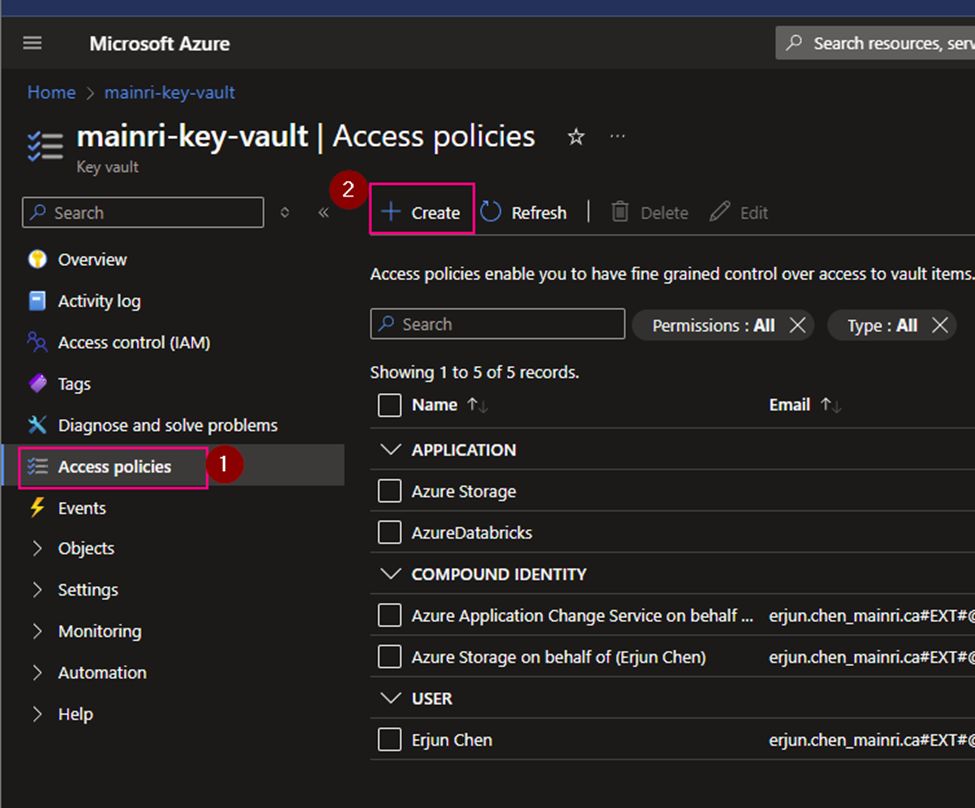
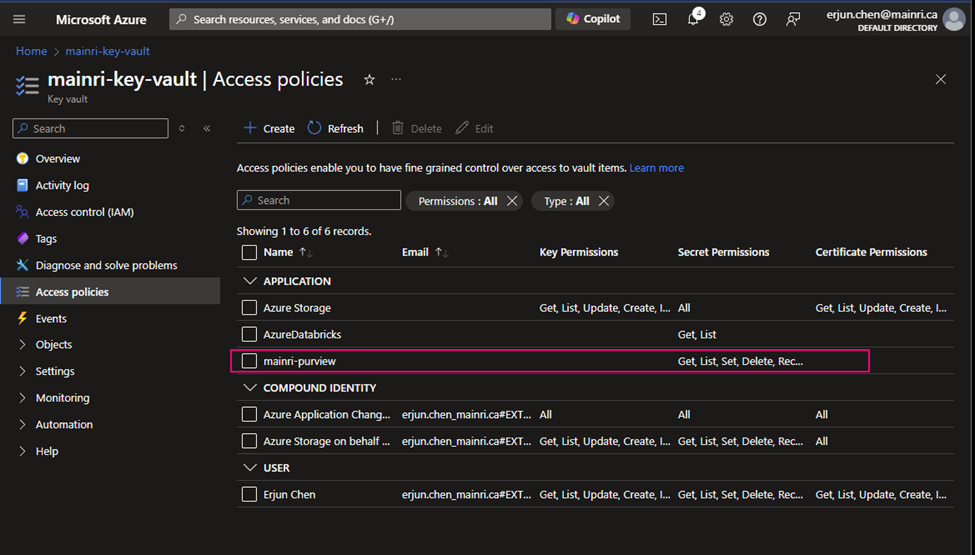
Using Access Policies create a secret
There is another way “Access Policies” to create a secret.
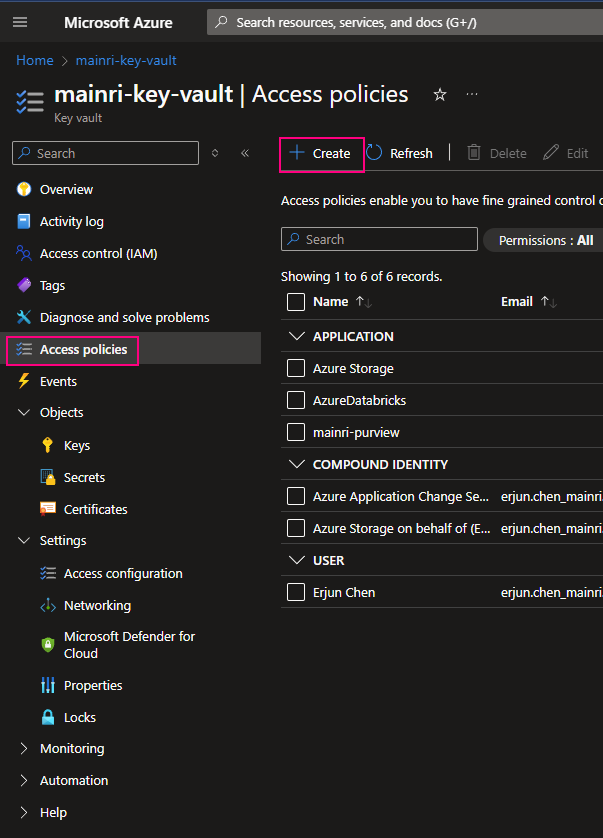
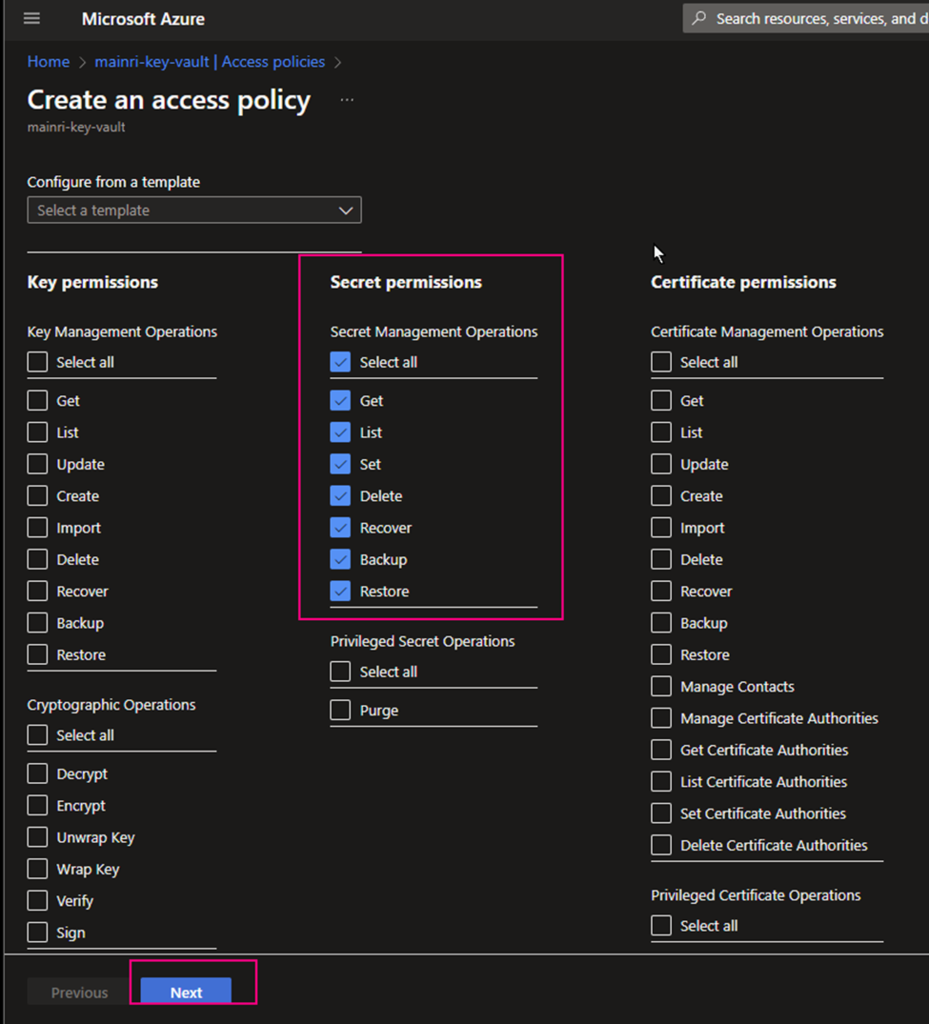
Select the permissions you want under Key permissions, Secret permissions, and Certificate permissions.
If you create a key secret for users to use in their application or other azure services, usually you give “get” and “list” in the “Secret permissions” enough. Otherwise, check Microsoft official documentation.
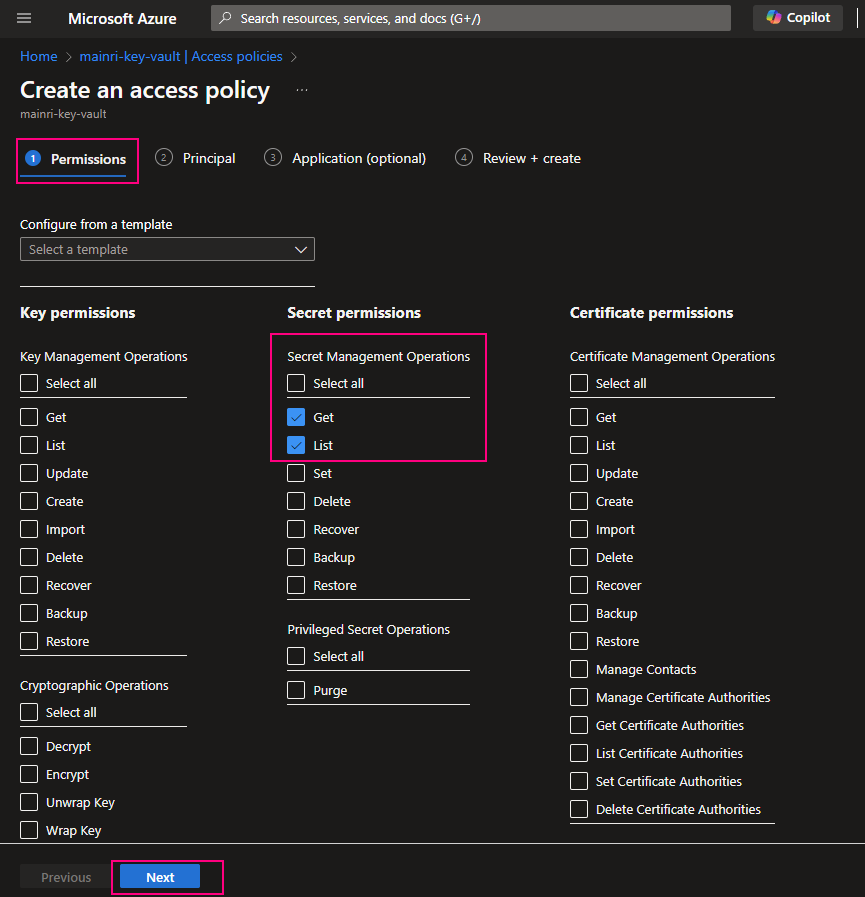
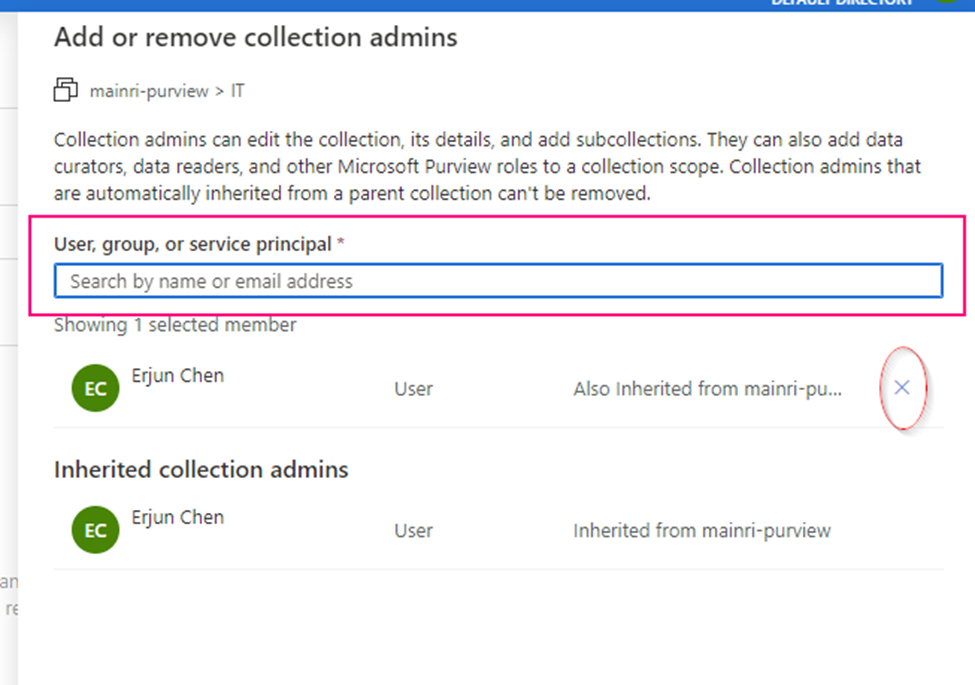
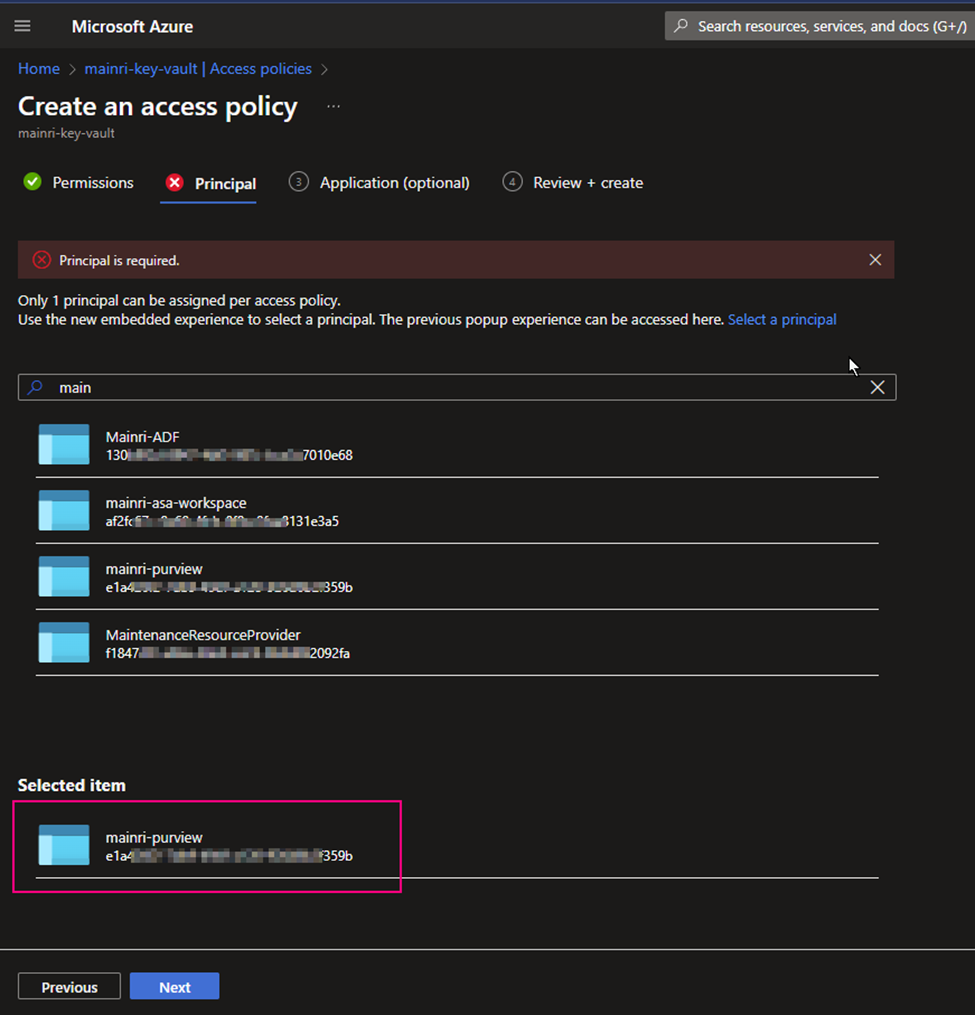
Under the Principal selection pane, enter the name of the user, app or service principal in the search field and select the appropriate result.
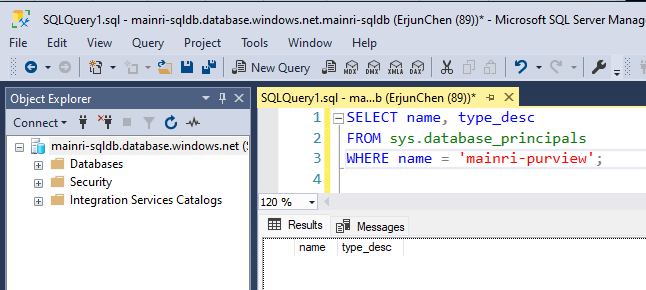
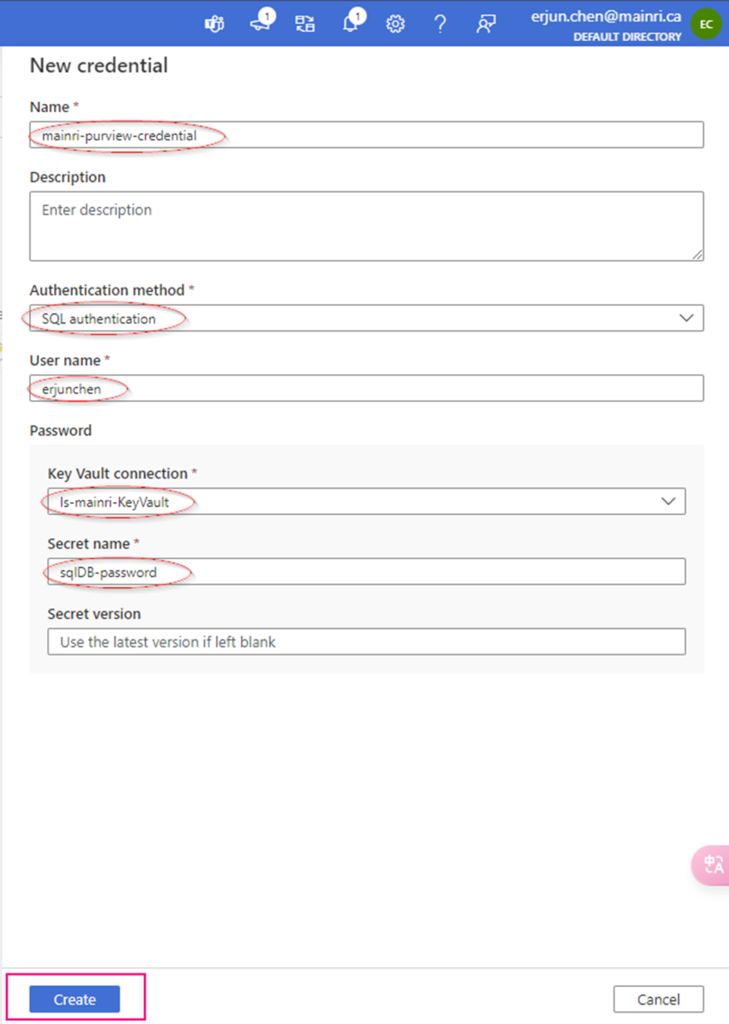
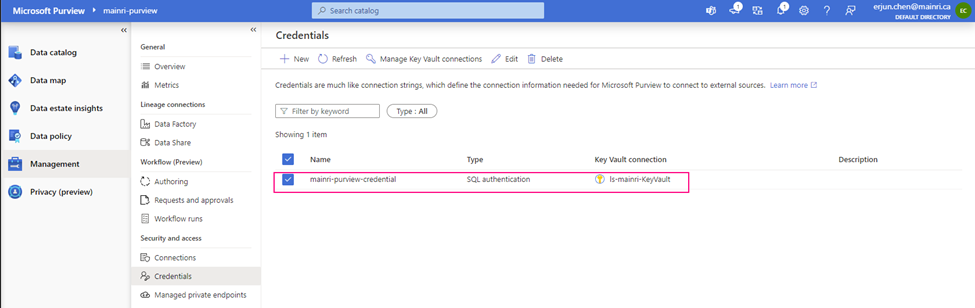
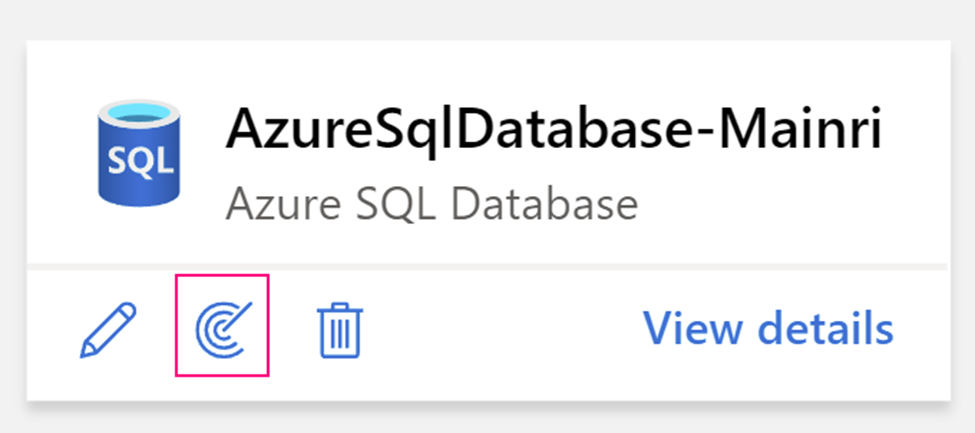
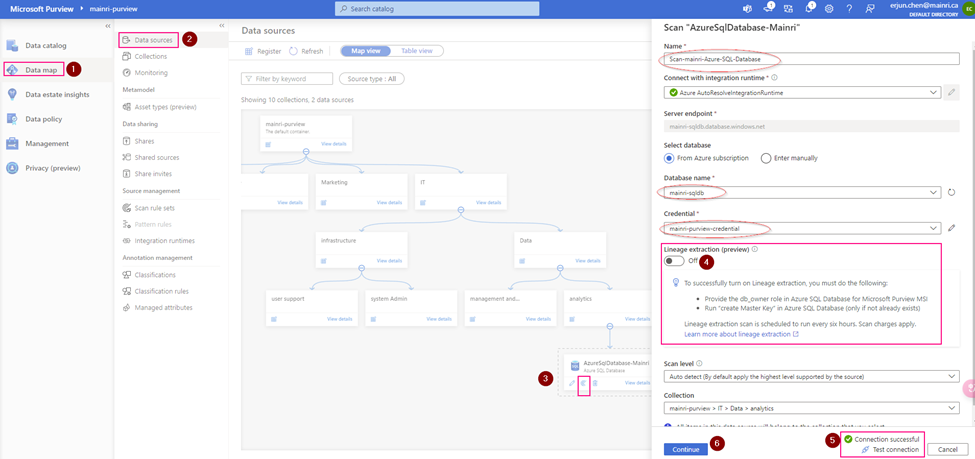
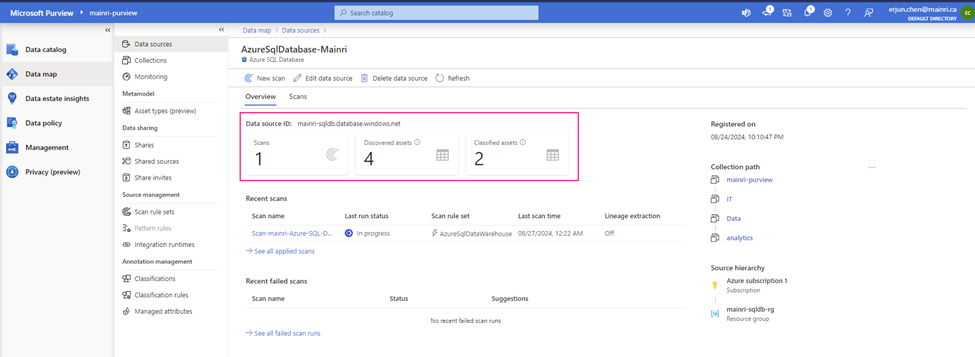
Using Azure SQL Database as an example
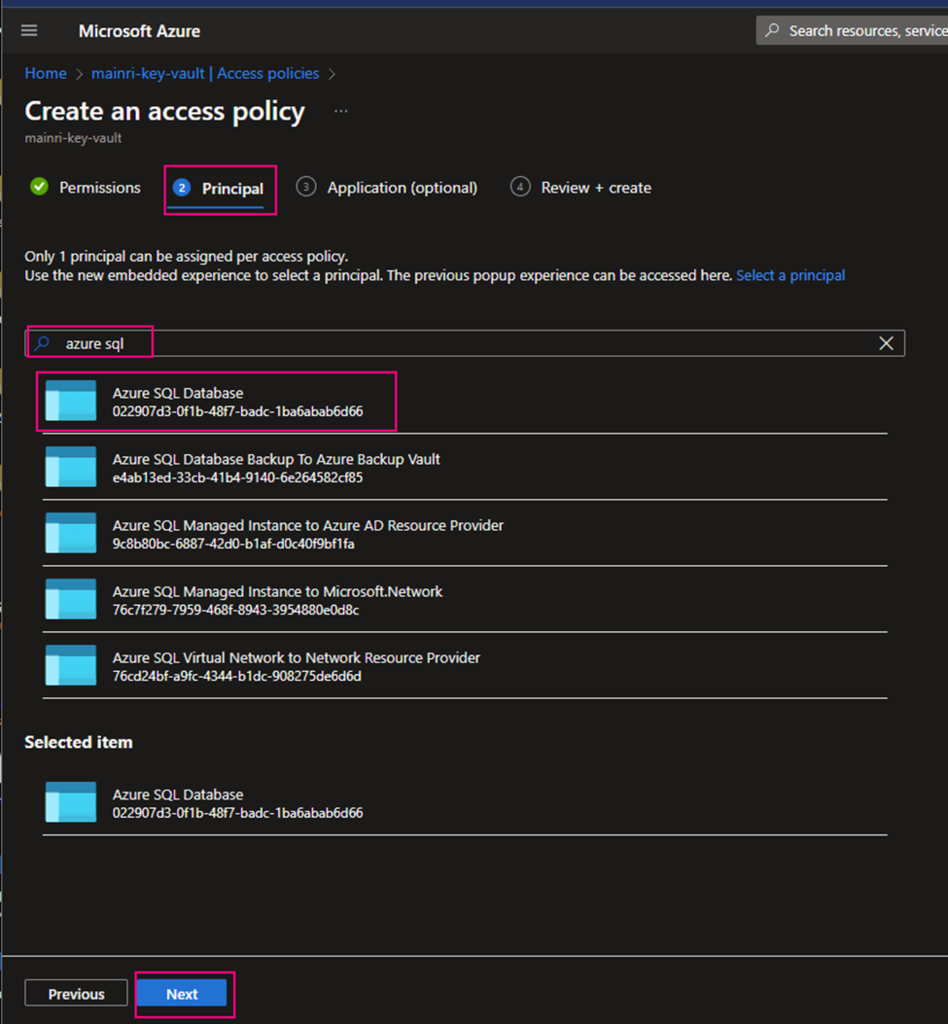
Caution: when you add principal, make sure you select right service instant. Especially you act as a infrastructure administer, your organization has multiple teams that they are independently using different service instants, e.g. different Synapse Workspace. select correct instant. I have been asked to help trouble shotting this scenario a few time. Azure admin says, he has added policies to key-vault, but the use cannot access there yet. that is a funny mistake made, he has added ADF to kay-vault policies, unfortunately, the ADF is NOT team A used, team B is using it. 🙂
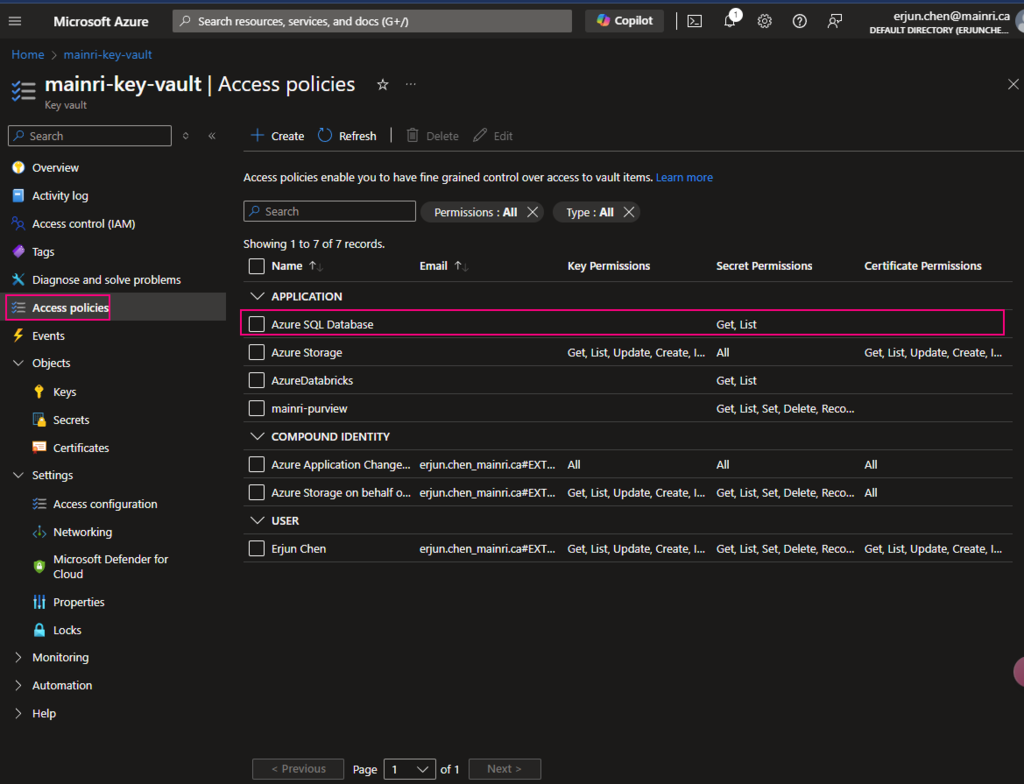
Back on the Access policies page, verify that your access policy is listed.
Create secret key and value
We have discussed it above. Need not verbose.
Done!
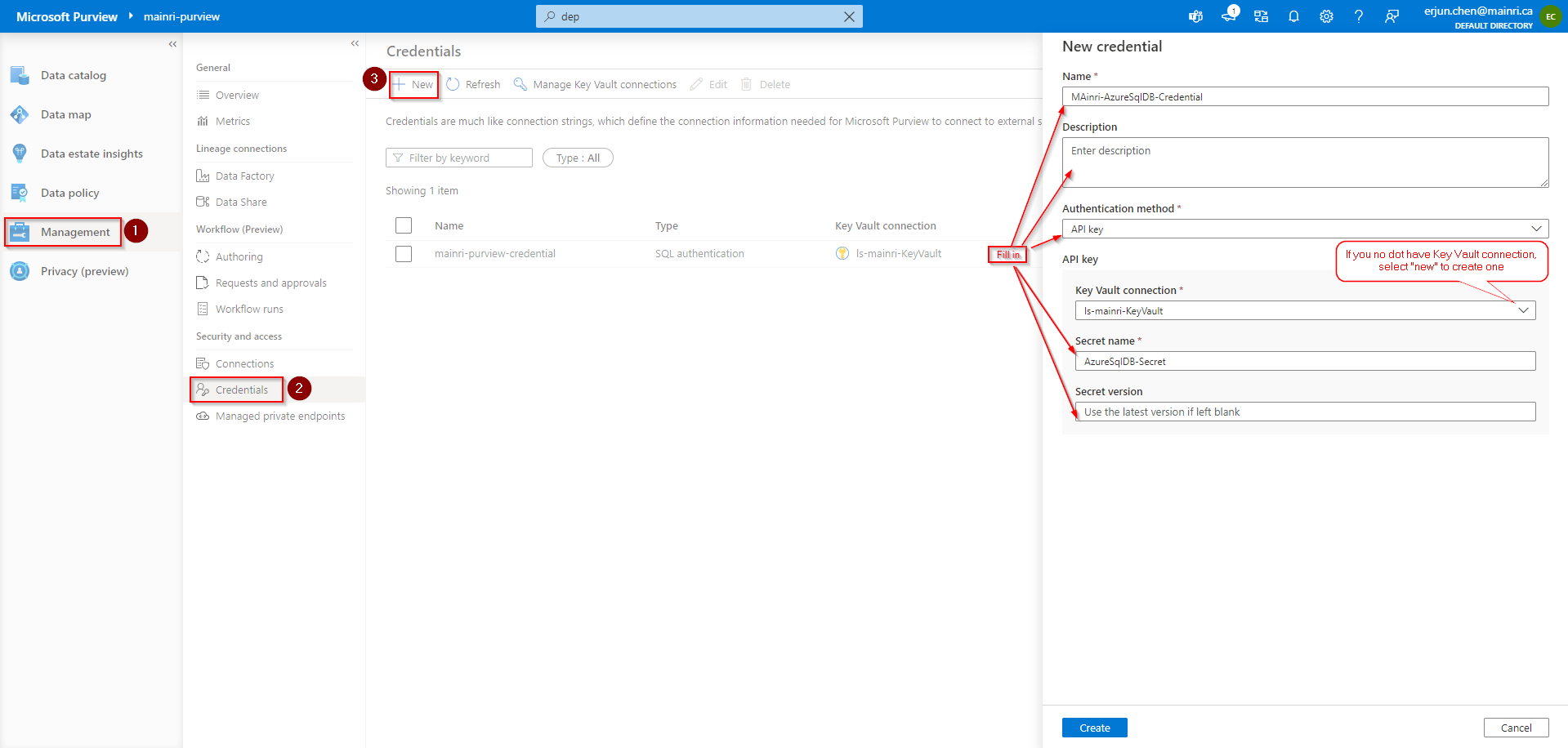
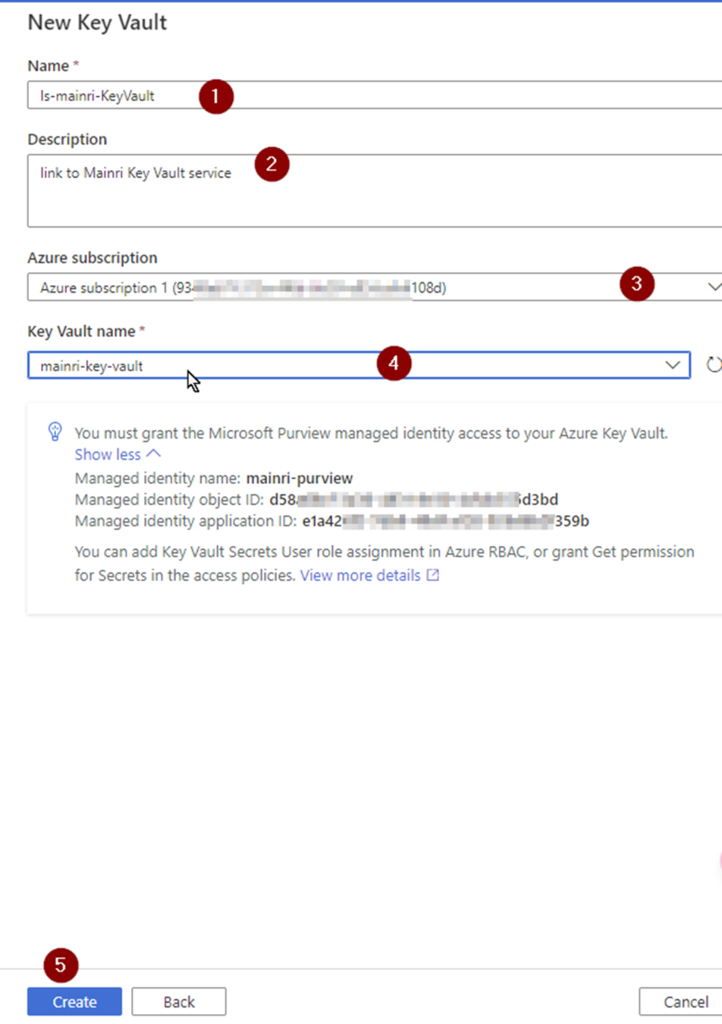
Using secrets that were saved in Key Vault
Using secrets usually have 2 major scenarios, directly use, or use REST API call to retrieve the saved secret value.
Let’s use Data Factory as an example to discuss.
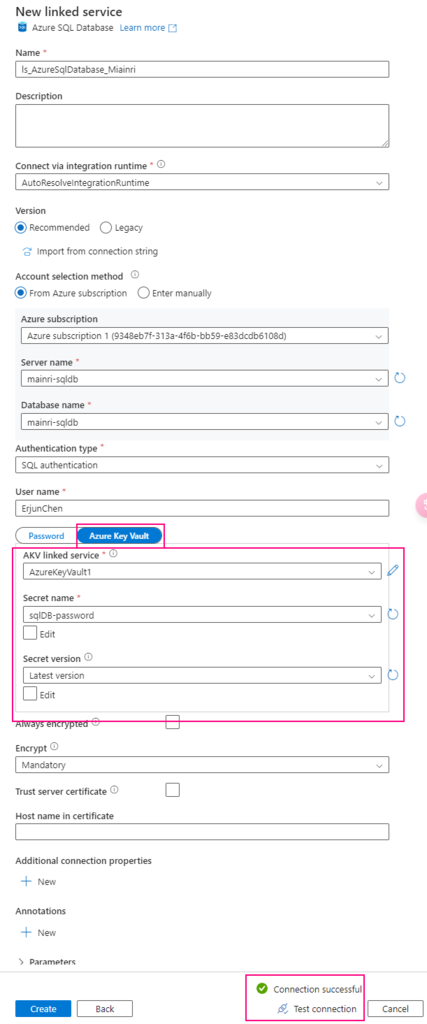
Scenario 1, directly use it
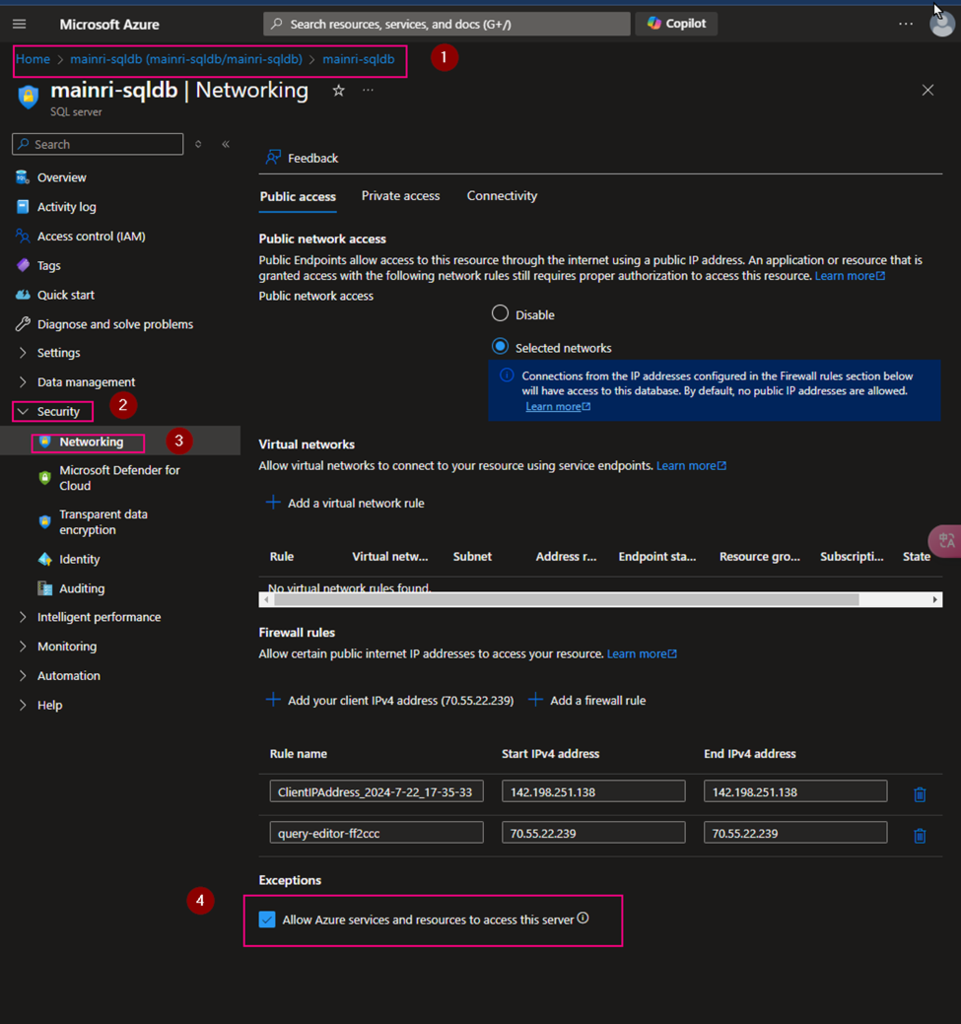
For example, when you create linked service to connect Azure Sql Database
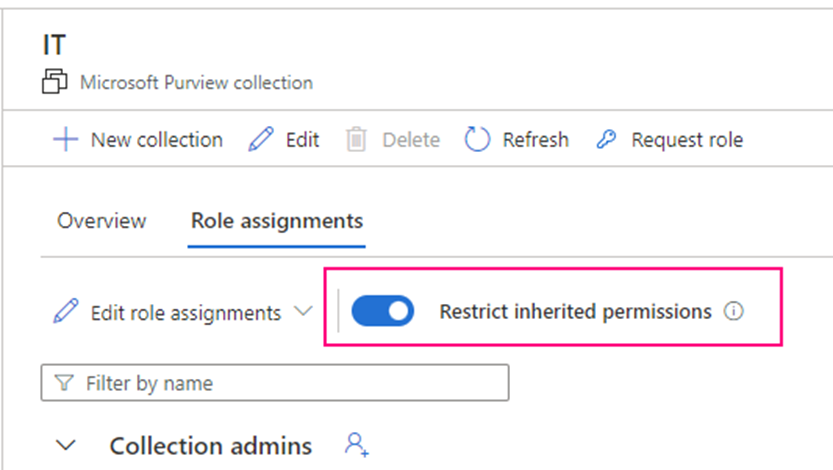
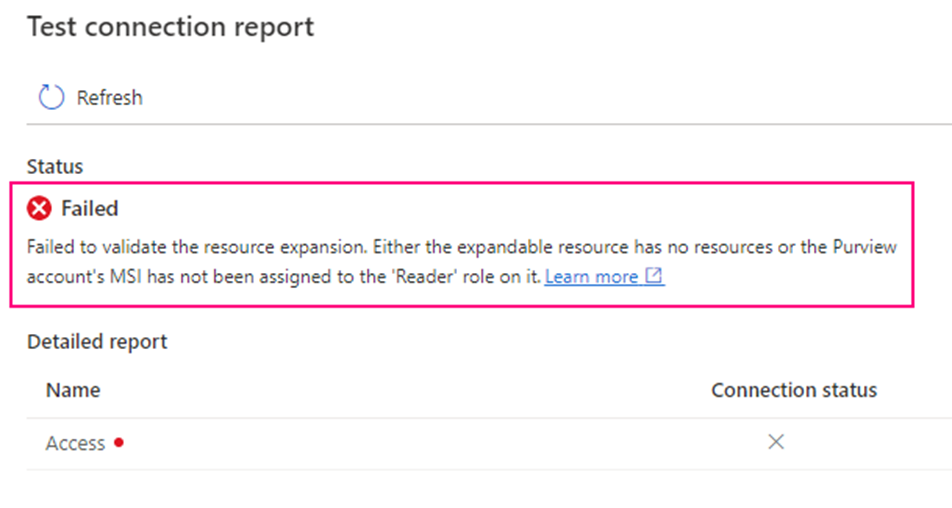
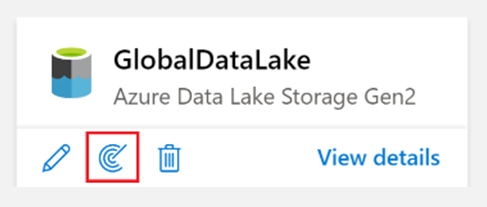
You have to make sure that Key Vault’s access policies has this ADF access policies, get and list
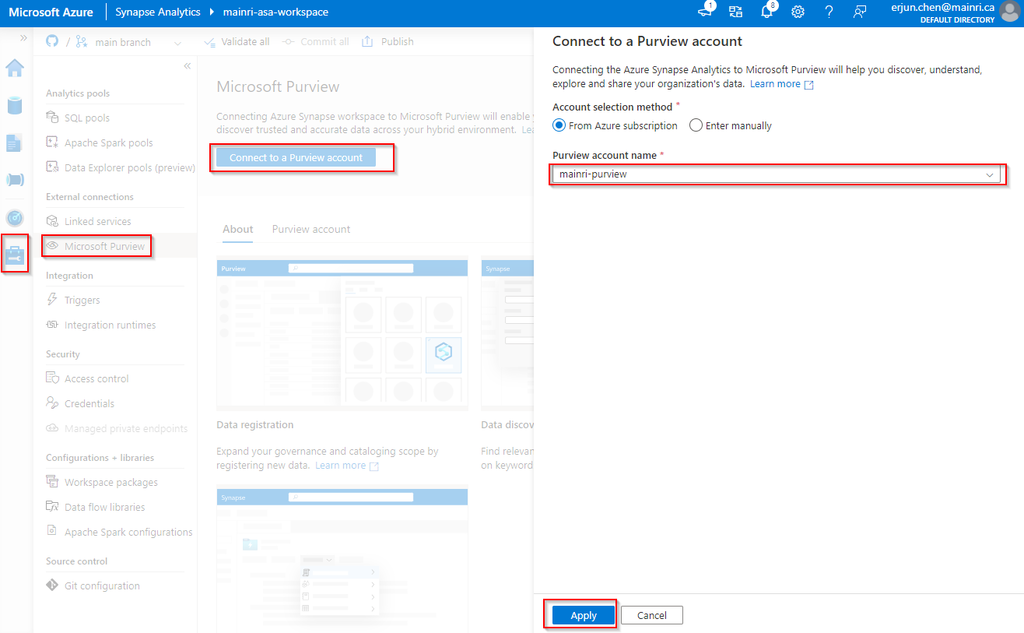
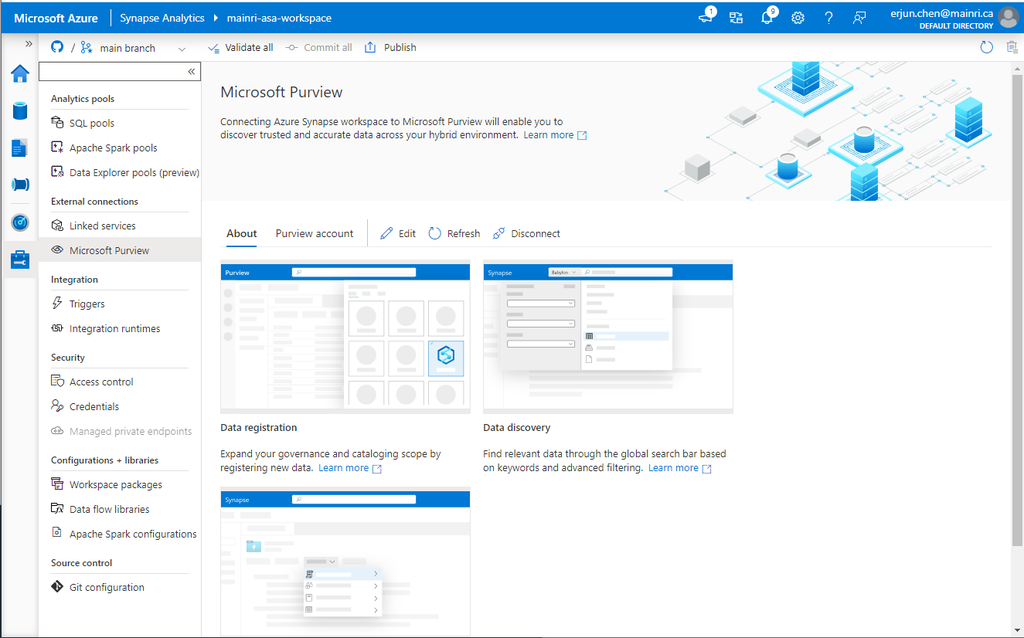
one more example, System workspaces use key-vault.
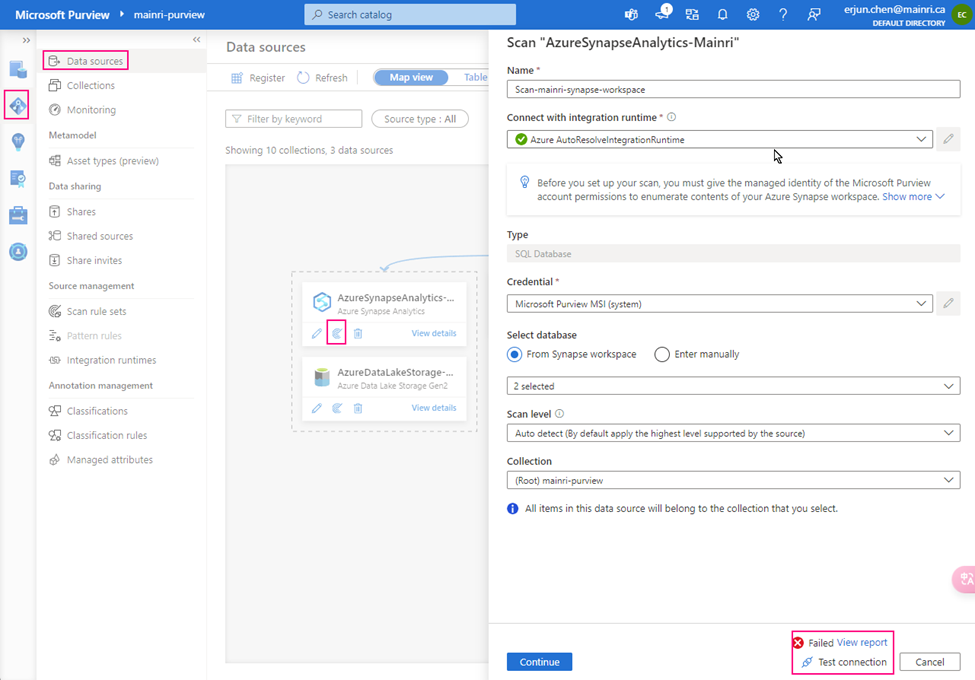
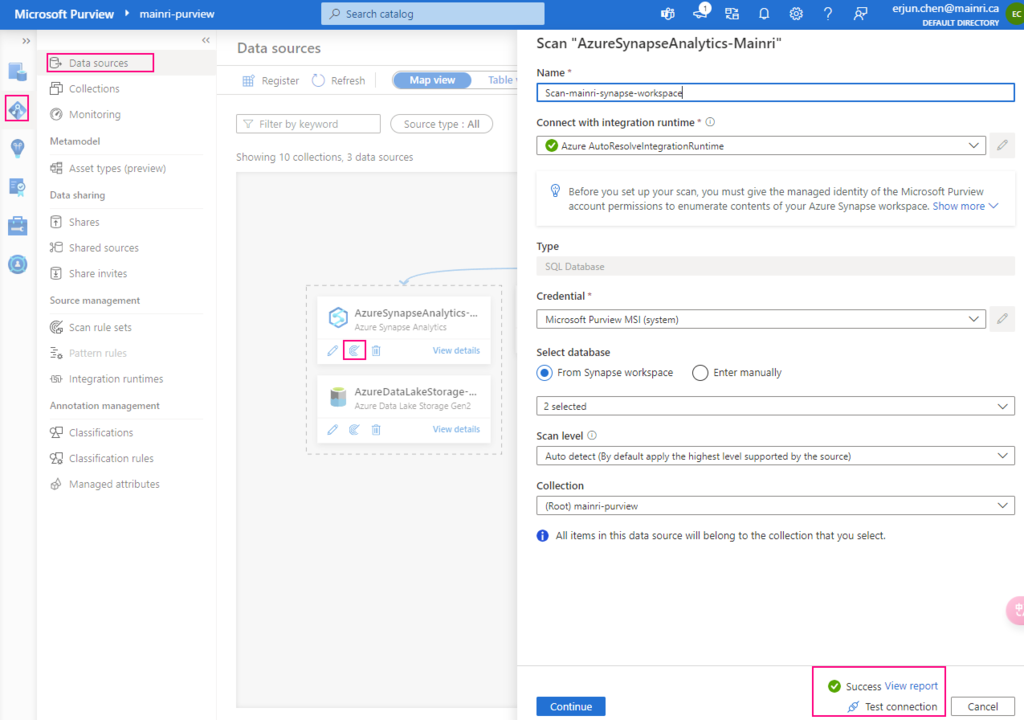
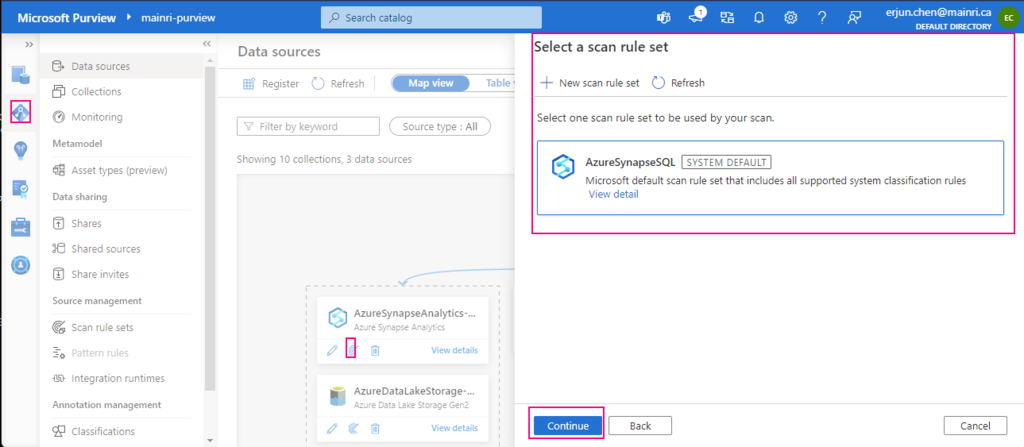
Once again, make sure your Synapse Workspace has access policies, “Key Vault Secrets User“, “get” and “List”

Scenario 2, REST API call Key Vault to use secret
Many engineers want to call the key Vault to retrieve the secret value for a certain purpose, e.g. Synapse pipeline to get SharePoint Online list or files that resident in SharePoint Library, you need an application secret value to build the query string. Normally, the application’s secret value is saved in Key Vault. In this case, you have to make a http call to Key value.
Get a specified secret from a given key vault.
The GET operation is applicable to any secret stored in Azure Key Vault. This operation requires the secrets/get permission.
GET {vaultBaseUrl}/secrets/{secret-name}/{secret-version}?api-version=7.4
for this example,
{vaultBaseUrl} https://mainri-key-vault.vault.azure.net
{secret-name} mySecretName
{secret-version} can skipped, if you skipped it, it will use “Latest Version”
Look at the pipeline
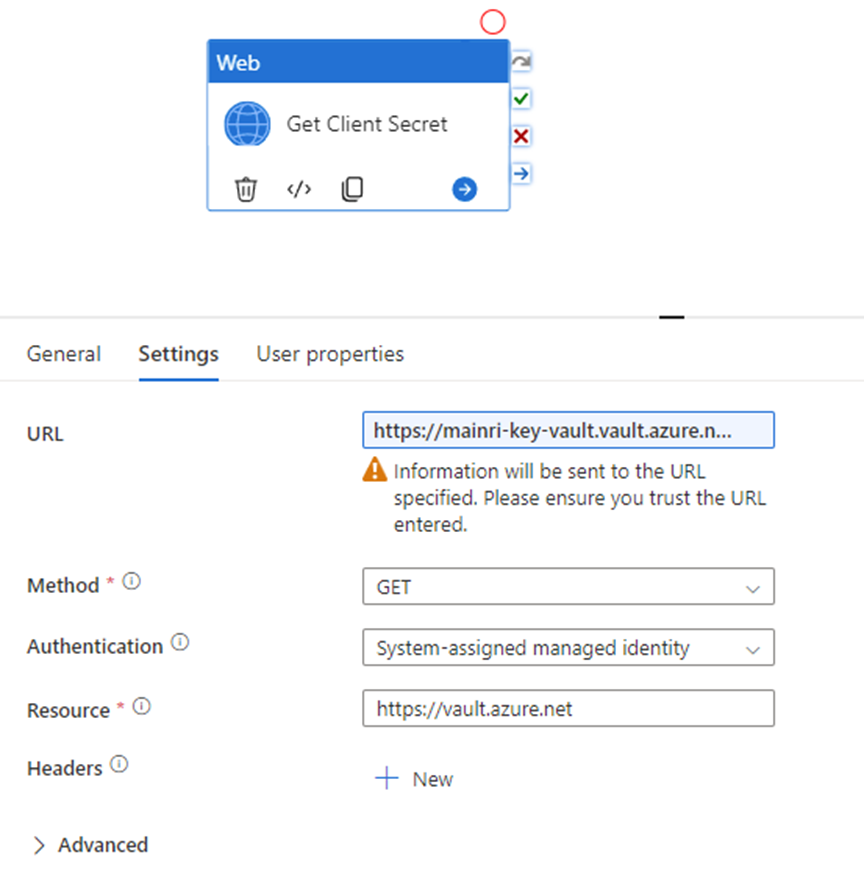
This web activity calls Azure Key Vault to retrieve secret value.
URL: https://mainri-key-vault.vault.azure.net/secrets/mySecretName?api-version=7.4
Method: Get
Authentication: Get
Resource: https://vault.azure.net
Caution, ?api-version=7.4 is very important, you have to add it to the URL.
all done.
Please do not hesitate to contact me if you have any questions at William . chen @ mainri.ca
(remove all space from the email account 😊)
Appendix:
MS document Get Secret – Get Secret